5 Security Strategies to Ensure Data Privacy in Healthcare
Privacy Concerns in the Healthcare Industry
Big healthcare data holds great promise for enhancing patient outcomes, forecasting epidemic breakouts, gaining insightful knowledge, avoiding preventable diseases, lowering healthcare delivery costs, and generally enhancing quality of life. However, choosing the appropriate applications for data while upholding security and patient privacy rights is a challenging task.
No matter how important big data is to the development of medical knowledge and how crucial it is to the success of all healthcare organizations, its implementation is still dependent upon security and privacy concerns being addressed.
It is imperative to take steps to protect patient information more effectively given the rising usage of medical software and the significance of health care data. While enhancing the safety of sensitive data has recently been a top priority, privacy has long been one of the major concerns with health care information technology. In this article, we will go over the top five security strategies for maintaining privacy in the healthcare industry.
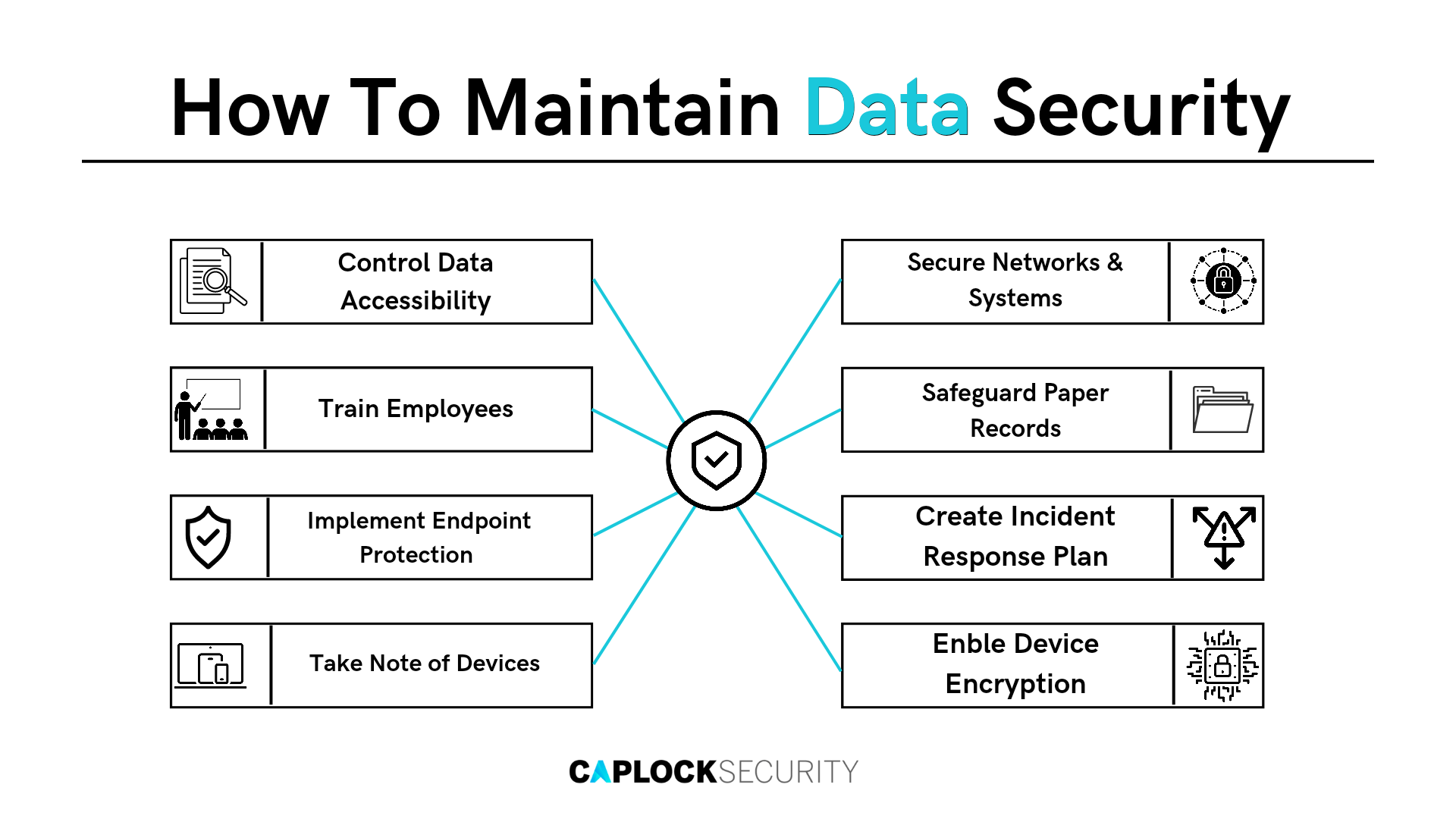
Security Strategies to Ensure Privacy
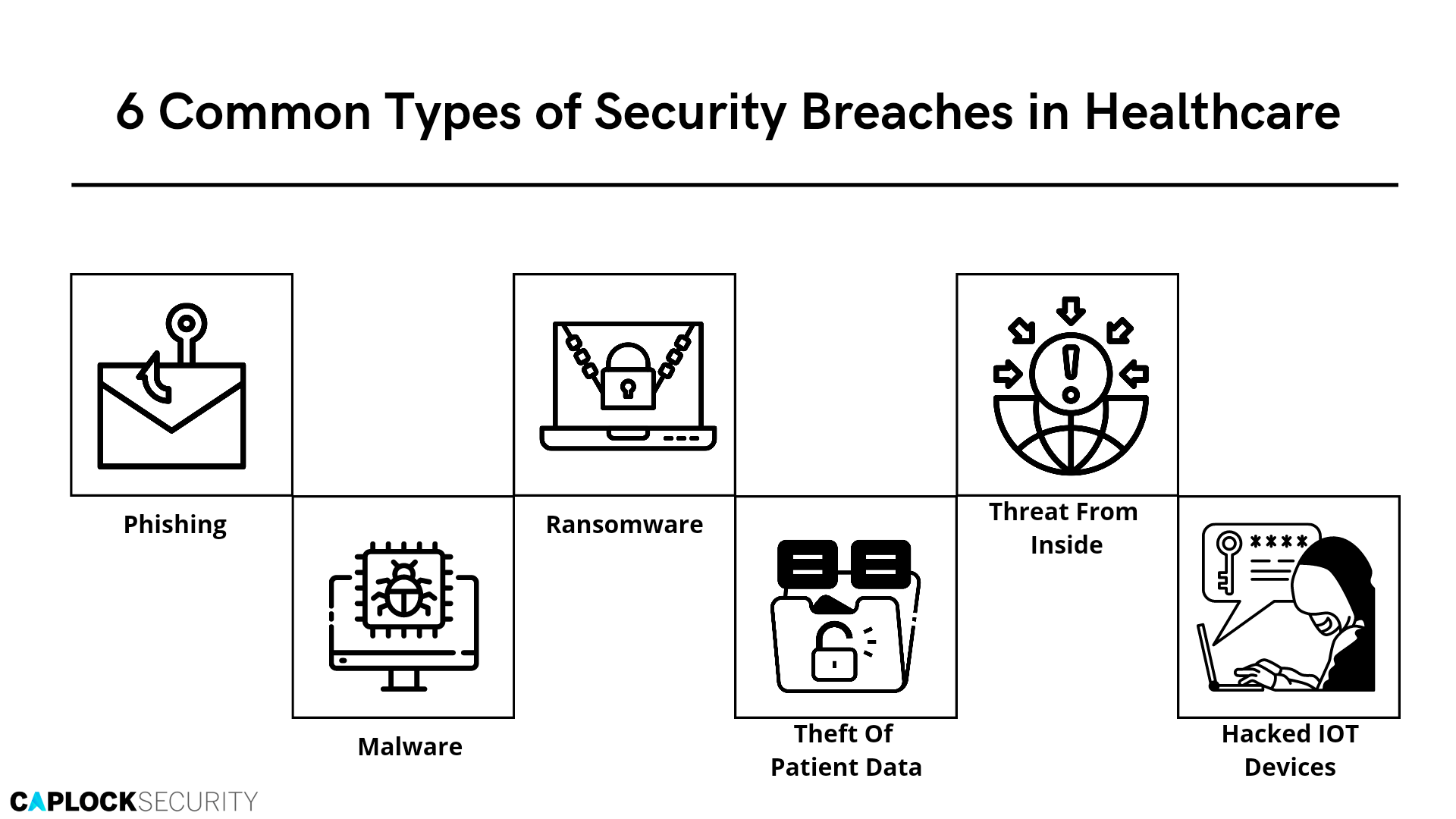
Companies are constantly searching for innovative and up-to-date methods to reduce the risk of their sensitive data. It is a common misconception to believe that switching your electronic health record (EHR) or electronic medical record (EMR) vendor will resolve the issue, yet this isn’t the most sensible course of action. Health IT still utilizes a number of manual procedures. Being compliant with HIPAA regulations isn’t always sufficient since hackers seek patient data due to it being a lucrative prospect. Organizations in the healthcare industry need to proactively secure their information through preventative manual procedures as well as software security implementation.
Communications Encryption and Network Security
Network Security
Just like having more devices makes you more vulnerable, having additional unprotected wireless connections does the same. The data is more susceptible if your practice provides free Wi-Fi for clients and a chat platform. Since organizations don’t have patient data on open networks, their security is frequently disregarded.
The creation of automated processes for updating users and devices is an excellent concept. This makes sure that former personnel no longer have access and that new technology is protected.
- Consider it crucial to keep your system up-to-date with any potential software changes when it comes to your health IT solution.
- A system is more vulnerable to hacking if updates are not made in a timely manner.
- Software upgrades generally improve system performance and solve tricky-to-use features.
Encryption
Healthcare facilities can take measures to further comply with HIPAA requirements, including data encryption. These relatively simple but essential procedures to help safeguard against a compromise include encrypting your health records, medical records, and other data, as well as making sure that devices are secure.
Since hackers won’t be able to decipher the code without a key, encryption automatically strengthens your cyber security perimeter. Every piece of financial and vital data is backed up and secured by an encryption code, keeping it safe in the event of a security breach. Hackers may target your hospital’s financial invoices and reports, patients’ sensitive information, and other medical facilities. Access-level restrictions can be used to protect the data and regulate who might access it.
Regulate Data Access
According to recent research, the healthcare sector has the largest percentage of insider risks of any sector, with 98% of firms susceptible to data breach incidents involving insiders. A good rule of thumb is that patient records should only be attainable on a need-to-know premise. This implies that a physician or support staff member should only have temporary access to specific patient information and shouldn’t have unlimited access to it.
Sample EHR (Electronic Health Data)
Education of end users about the security threats associated with health care data is a crucial step in ensuring security is maintained. If a security threat arises at any point, they will be better equipped to react quickly and forcefully. Patients can also take similar safety measures to guarantee the protection of sensitive data, such as ensuring that access to such data is password-protected and multi-factor authentication is provided.
Employee Awareness Training
The weakest link in your cyber-security procedures is typically the user. It’s crucial to educate staff members on data protection procedures, and this training should be consistent and continuous.
Insiders are frequently involved in security blunders. The HIPAA Journal reported that 712 health care data breaches were recorded between January 1 and December 31, 2021, which means that on average, 59 data breaches were reported each month in 2021. This breaks the previous record for health care data breaches by 70, or 10.9% more than in 2020. Such an act is typically preventable, and adequate training greatly reduces the likelihood of making mistakes of this nature.
Your personnel may be better able to identify potential security dangers and take better measures after receiving security awareness training. This kind of instruction can urge users to handle patient data with the required caution. All of your staff, both new and old, need to be trained on the most recent data security practices.
To further prevent unintentional data sharing with unauthorized personnel, disable file-sharing and remote printing, uninstall any unneeded software, and advise staff to refrain from downloading anything against organization policies.
Endpoint Protection & Data Awareness
Endpoints
To ensure the security of health care data, it is essential to monitor and manage every endpoint, regardless of the type and origin of a cyber assault. All potential endpoints are protected by solutions like application whitelisting, which also enables an organization to set access control procedures to reduce threats.
Furthermore, next-generation antivirus and antimalware solutions with artificial intelligence and deep learning capabilities to detect and eliminate viruses are preferable to traditional antivirus solutions because they are out-of-date. For comprehensive security, you may also combine the security solution with already in-use management solutions.
Data Awareness
Our world is becoming more populated with devices thanks to the Internet of Things. There are many laptops, tablets, cellphones, and other devices in use in today’s offices. Personal devices are increasingly the preferred method of business communication as more employees access company software via mobile applications. However, having additional gadgets access your data also increases its vulnerability.
Consider having your IT personnel evaluate the danger of each device that may access your data to lessen the likelihood of a security breach. Before allowing them admission onto the property, make sure they inspect even their personal tablets and smartphones. They are arguably more significant considering that, in contrast to gadgets used only for business, they are frequently more vulnerable.
To be clear, this does not entail looking through the personal data of your employees. You can and should investigate the security capabilities of each device accessing your data. If you haven’t already, get started right away. The more time you take, the more you’ll need to catch up, and the more exposed you and your data are.
Data Masking
Sensitive data elements are replaced with an incomprehensible value using masking. Since it is not a true encryption method, it is impossible to recover the original value from the masked value. It employs a technique known as de-identification, which involves masking or suppressing personal identifiers like names and social security numbers as well as extrapolating or suppressing semi-identifiers like date of birth and zip codes. Data masking is therefore one of the most commonly used methods for live data confidentiality.
Adding noise to the data, switching cells between columns, and replacing groups of x records with y copies of a single sample are some further privacy preservation techniques.
The reduced cost of protecting a big data deployment is indeed a key benefit of this strategy. Masking minimizes the requirement for implementing extra security controls on that data while it is stored in the platform while protected data is transferred from a routed source into the platform.
Importance of Security in Healthcare
It’s unarguably essential from a patient perspective compared to a health care organization’s standpoint to keep health care data secure. Patients want their health information to be kept private for their own privacy concerns, but medical facilities also need it for a variety of legal reasons, including doctor-patient confidentiality agreements.
Recall that patient data stored by health IT software includes information on their insurance, credit cards, and other personal documents in addition to medical records. If hacked, this individual carries the risk of experiencing identity theft as data can be taken and misused, as well as sold on the black market.
Outsourcing cybersecurity services and utilizing modern protection and monitoring technologies will assist in ensuring that your healthcare security plan is solid and that your customers’ data is secure, while freeing up your own personnel to focus on other business operations.
At Caplock Security, our staff consists of devoted security experts with years of experience in a range of cybersecurity disciplines. A number of our clients have already benefited from our support to raise their security standards, meet compliance criteria, and reduce risk. Our experts can help you identify your security weaknesses and can provide guidance on how to address them successfully.












