HIPAA Cybersecurity Compliance Essentials
What is HIPAA Compliance?
The Health Insurance Portability and Accessibility Act (HIPAA) is a regulation that aims to protect patient health information in the US. The security controls, methods, and procedures defined in the HIPAA regulation must be implemented by certain organizations that have access to protected health information (PHI).
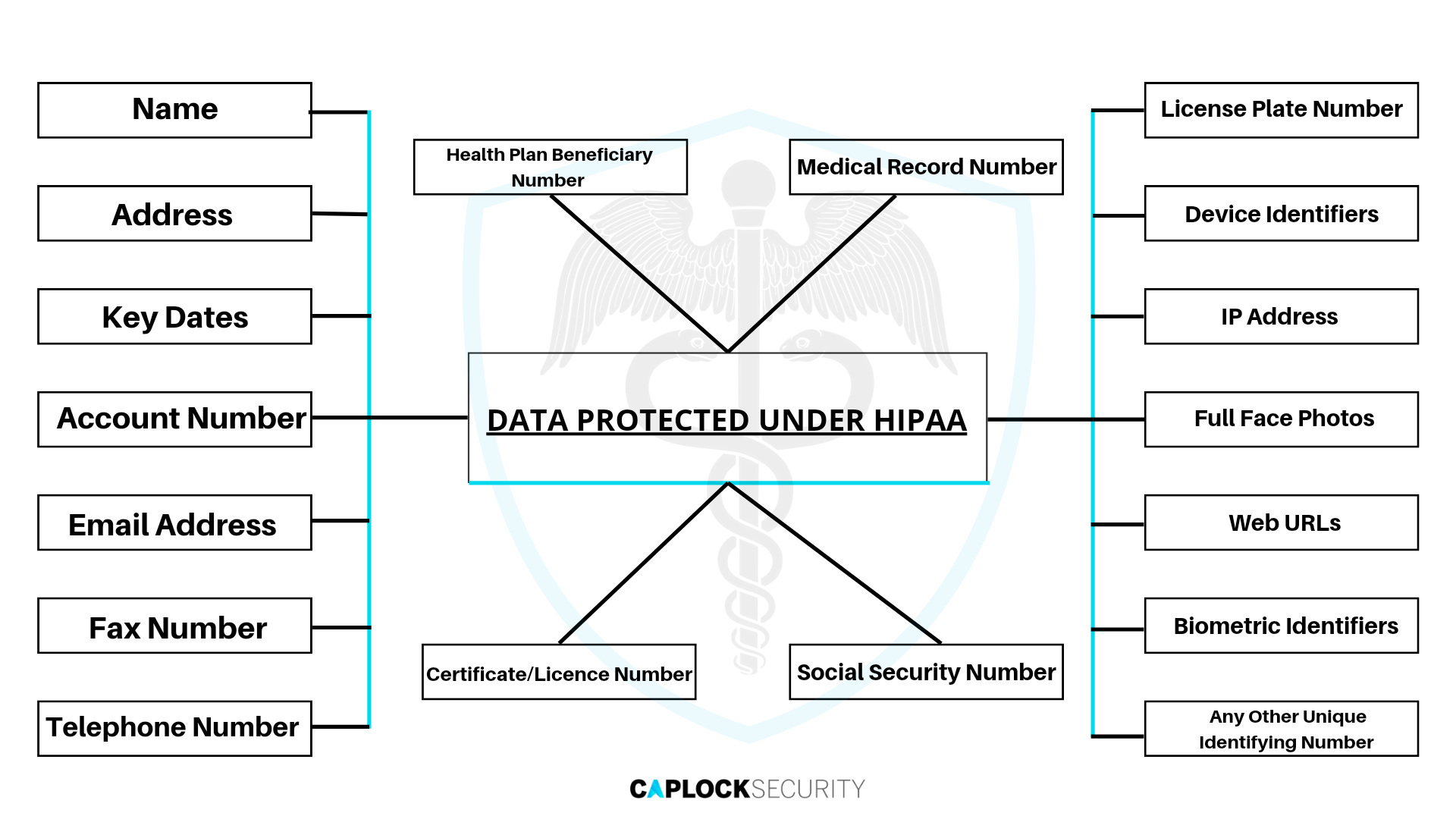
Sensitive patient health information, including treatment specifics, test results, personal identification information, and demographic data, is protected by HIPAA from being shared without the patient’s permission. The HIPAA Security Rule mandates that covered entities keep electronic protected health information (ePHI) secure and guarantee that their security can safeguard the organization from any kind of physical, administrative, or technical compromise in order to provide patients with the highest level of protection for their health records.
The Need for HIPAA Compliance
The Department of Health and Human Services (HHS) notes that HIPAA compliance is more crucial than ever as healthcare providers and other organizations that deal with PHI transition to computerized operations, including computerized physician order entry (CPOE) systems, electronic health records (EHR), and radiology, pharmacy, and laboratory systems. In a similar manner, health insurance offer access to applications for care management and self-service. All of these new practices boost productivity and mobility, but they also significantly raise security threats for healthcare data.
HIPAA Privacy Rule Requirements
The Privacy Rule, which sets standards for the privacy of personally identifiable health information, prescribes how healthcare companies are required to secure particular categories of patient information. Cases in which PHI may be accessed and disclosed are specified by the Privacy Rule. Additionally, it outlines the security measures that covered companies must put in place to protect PHI and grants patients specific rights with regard to their PHI.
- Privacy Policy : Covered entities must create and put into effect documented privacy policies and procedures that are compliant with the Privacy Rule.
- Personnel responsible for privacy: Covered entities must appoint a privacy official to formulate and carry out their privacy policies and procedures, as well as a contact person or contact office to take complaints and disseminate information on privacy practices.
- Training and management of the workforce: In order for all workforce members to perform their duties, they must get the necessary and suitable training on the covered entity’s privacy policies and procedures.
- Mitigation: Covered entities are required to make an effort to lessen any negative consequences that may have resulted from employees or business partners using or disclosing PHI in ways that are against their privacy policies and procedures or the Privacy Rule.
- Data Protection: Covered entities are required to maintain reasonable and suitable administrative, technological, and physical protections to stop the use or disclosure of PHI, whether on purpose or accidentally.
Complaints: Covered entities must establish channels for people to file grievances regarding their adherence to the Privacy Rule and their privacy policies and practices. Entities must, among other things, specify where people can file complaints and inform complainants that they can do so to the Secretary of HHS.
Retaliation and waiver: covered entities are not permitted to take adverse action against a person who exercises their right to privacy under the Privacy Rule, who cooperates with an investigation by HHS or another relevant agency, or who objects to a policy that they believe violates the Privacy Rule.
Documentation and record-keeping requirements: Covered entities must keep track of their privacy practices notices, policies, complaints resolutions, and other actions, activities, and designations that the Privacy Rule requires to be documented for a period of six years following the later of the creation date or last effective date.
HIPAA Security Rule Requirements
The Security Rule empowers authorized entities to embrace innovative technology that improve the effectiveness and quality of patient care while still safeguarding the privacy of individuals’ health information. By design, the Security Rule is adaptable enough to let a qualified business use policies, practices, and technology that are appropriate for its size, organizational structure, and e-PHI security threats.
Risk Analysis and Management
The HIPAA Security Rule requirements for administrative safeguards start with a risk analysis. According to the HIPAA Security Rule, a proper risk analysis needs to take the following into account:
- A risk analysis that contains incident probabilities and circles of impact
- Ensure that security measures are put in place to fix issues discovered during risk analysis
- Provide a list of security procedures along with a justification for their use
- Enable security safeguards that are constant, acceptable, and essential
Checks should be made on a regular basis to make sure the risk analysis is taking into account and identifying security incidents, monitoring access to patient and staff information, and assessing if the security measures in place are enough to limit risk.
Administrative Safeguards
- The Process for Security Management
All entities are required to identify and analyze data that poses a risk to protected information in accordance with the HIPAA Security Rules, then put security measures in place to reduce that risk. - Security Officers
A security professional who is in charge of creating and carrying out security policies and procedures must be designated by a covered company. - Access Control and Management
The HIPAA Privacy Rule states that only authorized staff are permitted access to private information when it is judged necessary on behalf of the patient or in the protected person’s best interests. Workforce Management and Training
All protected information may only be accessed by those who are qualified and authorized, or who are under their supervision. The HIPAA Security Rule requirements call for the training of individuals in security and process policies as well as the adoption, enforcement, and use of sanctions against those who violate these policies and procedures.Evaluation
Your organization will need to regularly examine its security policies and procedures to make sure they adhere to HIPAA Security Rule standards in order to comply with HIPAA Security Rule regulations.
Physical Safeguards
- Access Control and Facilities
Entities subject to the HIPAA Security Rule requirements must ensure that only authorized personnel have access to protected information by preventing unauthorized access. - Security for Workstations and Devices
The HIPAA Security Rule’s security rules and procedures require the proper usage and accessibility of workstations and remotely accessible media. The transmission, transfer, disposal, secondary use, and removal of protected, electronically stored information must also be governed by policies and procedures.
Technical Safeguards
Access Management
The HIPAA Security Rule restricts authorized personnel from having access to protected information.Auditing measures
Gadgets that record personal information or are utilized in examinations, including hardware, software, and devices, must all be secure.Integrity
Entities subject to the HIPAA Security Rule requirements must have policies and procedures to guarantee that private and sensitive data is destroyed appropriately and is not improperly altered.Communication Security
The use of safeguards to stop unauthorized access to protected information transferred electronically is a requirement for covered entities.
Organizational Requirements
- Accountabilities of Covered Entities
Until the infringement has been fixed, knowledge of any security breaches or violations of privacy policies and procedures must be continually managed. Violations are violations in and of themselves if they are not properly handled or adequately protected against in the future. - Business Partner Agreements
In accordance with the HITECH Act of 2009, HHS created regulations for business associate contracts and duties.
Policies and Procedures
Reasonable policies and procedures must be adopted in order to comply with the HIPAA Security Rule requirements. Records must be properly stored and protected for six years from the date they were created or the last effective date that the written security policies and procedures of the affected policies required specific actions, activities, or assessments.
- Updates: The HIPAA Security Rule requires periodic reviews and updates to documentation when changes occur at environmental or organizational levels that may alter the security of the protected information.
Consequences of HIPAA Violations
Covered organizations must adhere to HIPAA regulations, and failure to do so might lead to penalties. HIPAA categorizes violations into four levels:
Tier 1: If the covered entity made a good faith effort to comply with HIPAA’s requirements but was uninformed of the violation, the violation could not reasonably have been avoided. Penalties can be as high as $50,000.
Tier 2: Despite the covered entity’s best efforts to comply with HIPAA, the breach went unnoticed despite their knowledge of it. The range of fines is from $1,000 to $50,000.
Tier 3: The covered entity made an effort to fix the “willful neglect” of HIPAA standards that led to the violation. The range of fines is from $10,000 to $50,000.
Tier 4: The violation happened as a result of “willful disregard” and the covered entity did nothing to make it right. Starting fines are $50,000.
Most HIPAA infractions include the unintentional or deliberate disclosure of PHI. HIPAA infractions that are frequent include:
- Stolen or lost devices
- Viruses such as ransomware
- Hacked user credentials
- Data sharing by accident on social media, email, etc.
- Physical trespass into a workplace
- Electronic health records breach (EHR)
Conclusion
The HIPAA Security Rule governs several facets of the healthcare sector, including patient information and health insurance programs. The system currently collects the majority of its data electronically, and all of its components must adhere to the HIPAA Security Rule in order for the system to operate in accordance with HIPAA standards.
HIPAA’s main objective is to safeguard the PHI given to covered companies and their business partners. Organizations are required under the HIPAA Privacy and Security Rules to manage and track PHI access and safeguard it from unauthorized access.
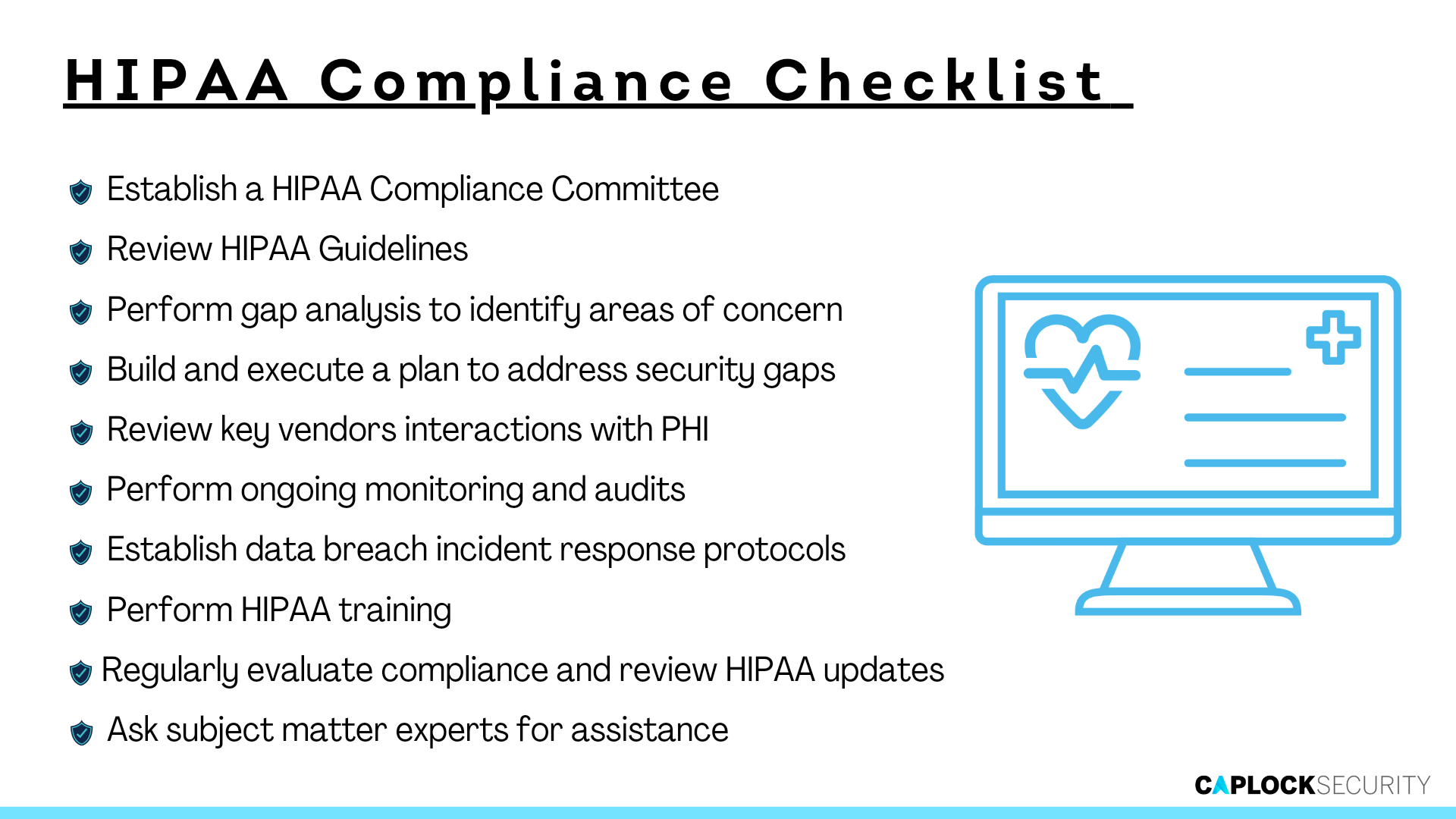
Caplock Security offers a variety of solutions that help healthcare providers and other organizations achieve compliance with HIPAA and other regulations. Bring the best out of your organization by relying on our cybersecurity professionals for tasks such as:
- Identifying unknown flaws or vulnerabilities that can result in a breach or disclosure.
- Validating, understanding, and preparing for known risks to your organization.
- Updating and maintaining regulatory or compliance controls.
- Providing clear, action-oriented recommendations designed to provide time-to-value in improving your security posture.
Prevention is superior to cure. Avoid the costly mistake of neglecting your organization’s cybersecurity aspect. Caplock Security gives you all the tools you need to streamline your security deployment without sacrificing performance, allowing for a unified strategy for efficient operations and getting you ready to scale for corporate expansion.