Implementing Zero Trust Architecture (ZTA) in the Age of Remote Work
Remote work has become the norm for many organizations, allowing employees to work from anywhere and access sensitive data remotely. However, this digital transformation has also introduced new security risks, making it crucial for businesses to implement robust security measures to protect their sensitive data.
Traditional security models that rely on implicit trust are no longer sufficient in the face of sophisticated cyber threats. This has led to the rise of Zero Trust Security, a proactive and adaptive approach that challenges the notion of trust and emphasizes verification at every step.
In this article, we will explore the importance of implementing Zero Trust Security in the age of remote work, discuss steps of implementation, and highlight the challenges of adopting this security approach.
The Importance of Zero Trust Security in Remote Work Environments
Remote work scenarios present unique challenges for traditional perimeter-based security approaches. With employees accessing sensitive data from various devices, networks, and locations, relying solely on perimeter defenses is no longer sufficient.
The limitations of such traditional security approaches include:
- Inadequate Verification of Trust: Traditional perimeter-based security measures often rely on static trust assumptions, such as assuming that users and devices within the corporate network are trusted. However, in remote work environments, users may connect from unsecured networks or use personal devices, which may not be adequately verified for trustworthiness.
- Limited Control over Access: Perimeter-based security approaches often grant broad access permissions once users are authenticated, which may result in over-privileged access to sensitive data. In remote work scenarios, this lack of granular control over access can increase the risk of data breaches, insider threats, and unauthorized access to critical resources.
Real Examples of Remote Work Hacks
Several high-profile cyberattacks targeting remote work environments have highlighted the critical need for robust security measures.
- In 2021, Hong Kong was targeted by watering hole attacks, as identified by Google’s Threat Analysis Group. Users who visited media and pro-democracy websites in Hong Kong were specifically targeted. Upon successful infiltration, the malware installed a backdoor on Apple devices, potentially gaining unauthorized access to sensitive information.
- Evilnum (APT TA4563) is a hacking group targeting financial institutions with a focus on fintech platforms. Their attacks involve spear-phishing emails with malicious Word documents, obfuscated JavaScript, and custom-built malware. Their goal is to create backdoors, capture data, and exfiltrate it in encrypted form.
These incidents demonstrate the vulnerabilities of remote work environments and the potential damage that cyberattacks can cause.
What is Zero Trust Security?
To address these limitations, organizations need robust security measures that verify trust and control access for all users, devices, and data, regardless of their location. This is where the concept of zero trust security comes into play.
Zero trust security is a proactive approach that ensures all users and devices are authenticated, authorized, and continuously verified before being granted access to sensitive resources.
Enhance Verification of Trust
ZTA leverages multiple factors, such as user identity, device health, location, and behavior, to dynamically assess trustworthiness and verify access requests. This enables organizations to have a more comprehensive and dynamic approach to trust verification, even in remote work scenarios.
Implement Granular Access Controls
Zero trust security enforces the principle of least privilege, granting users access to only the resources they need to perform their job functions, and nothing more. This helps organizations limit the potential damage of a data breach or insider threat by minimizing the exposure of sensitive data to unauthorized users.
Benefits of Zero Trust Architecture
ZTA is designed to address the evolving threat landscape and the challenges posed by remote work environments, by continuously verifying trust and controlling access to sensitive resources. Here are a few key benefits of implementing a Zero Trust Architecture (ZTA):
- Protecting Sensitive Information – Remote work environments can leave sensitive information exposed to potential cyber threats. Employees may use personal devices, connect to unsecured networks, or share data across various platforms, increasing the risk of unauthorized access or data breaches. Zero trust security helps organizations maintain accountability by implementing strict access controls, regardless of the user’s location or device.
- Mitigating Cyber Risks – With the growing sophistication of cyber attacks, relying solely on perimeter-based security measures is no longer sufficient. Zero trust security takes a proactive approach by continuously verifying user identities, assessing the trustworthiness of devices, and restricting access based on the principle of least privilege. This helps mitigate the risks of unauthorized access, data breaches, and other cyber threats in remote working environments.
- Ensuring Compliance and Auditing – Organizations are often subject to regulatory requirements and industry standards that mandate the protection of sensitive data. Zero trust security helps ensure compliance by implementing granular access controls, monitoring user activities, and generating audit logs for tracking and reporting.
- Adapting to Changing Work Environments – The nature of remote work is dynamic, with employees accessing data from various devices, networks, and locations. Zero trust security is designed to adapt to these changes, providing a consistent security posture regardless of where employees are working.
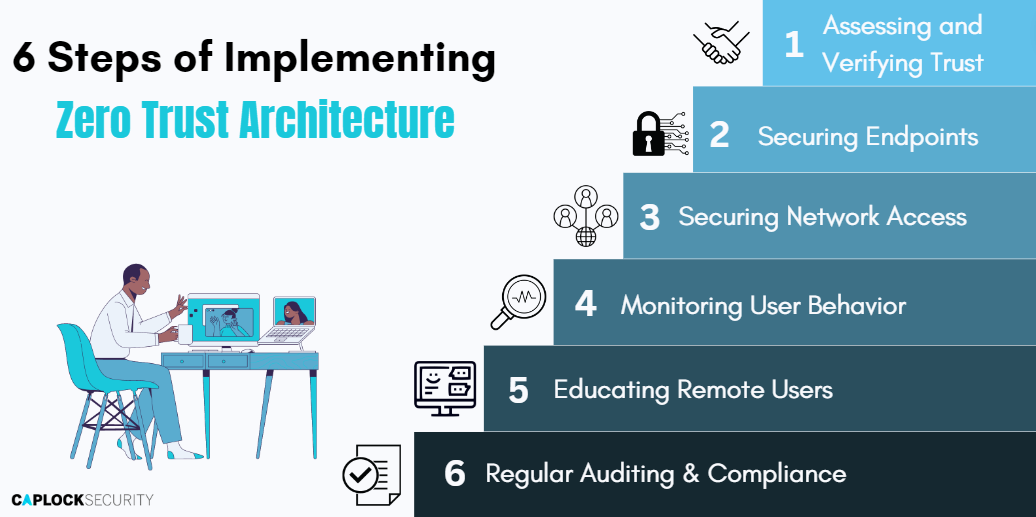
6 Steps of Implementing Zero Trust Architecture in Remote Environments
In this section, we will outline five actionable steps that organizations can take to successfully implement ZTA in their remote work environments, mitigating risks and enhancing cybersecurity posture.
1. Assessing and Verifying Trust
One of the key principles of Zero Trust Security is the need to verify trust for all users and devices, regardless of their location. To achieve this, organizations need to implement various security measures that assess and verify the trust of all users and devices attempting to access sensitive resources. Here are some actionable points that organizations can take to implement trust verification:
Identity and Access Management
Implement Identity and Access Management (IAM) solutions that provide granular access controls and allow organizations to enforce policies that determine who can access specific resources based on their identity and other contextual factors, such as location, device, and time of day.
User Behavior Analytics
Deploy User Behavior Analytics (UBA) solutions that leverage AI and machine learning algorithms to analyze user behavior patterns and identify anomalous or suspicious behavior that may indicate a potential security threat.
Continuous Authentication
Implement Continuous Authentication (CA) measures that constantly monitor user activity and require additional authentication steps or access restrictions if an unusual activity is detected. CA solutions, such as multi-factor authentication (MFA), can help ensure that only authorized users can access sensitive resources.
Device Security
Implement strong device security measures, such as endpoint protection and encryption, to prevent unauthorized access or data breaches from lost or stolen devices.
2. Securing Endpoints
Securing endpoints is a critical aspect of implementing Zero Trust Security in remote work environments. Endpoints, including laptops, desktops, smartphones, and other devices used by remote workers, can be vulnerable to cyber threats.
Here are key steps to secure endpoints:
- Require all remote devices to have up-to-date antivirus software, firewalls, and security patches
Ensuring that all remote devices have the latest antivirus software, firewalls, and security patches is essential to protect against known vulnerabilities and malware attacks. Regular updates should be enforced to address emerging threats and vulnerabilities. - Implement endpoint detection and response (EDR) solutions
EDR solutions provide advanced threat detection and response capabilities, allowing organizations to identify and respond to potential threats in real-time. These solutions can detect abnormal behavior, malicious activities, and other indicators of compromise on remote devices, enabling swift action to mitigate risks. - Use Mobile Device Management (MDM) solutions
MDM solutions enable organizations to enforce security policies on remote devices, such as strong password requirements, encryption, and remote wipe capabilities in case of device loss or theft. This helps to ensure that remote devices are configured and secured according to organizational security standards, reducing the risk of unauthorized access or data breaches.
3. Securing Network Access
To maintain a Zero Trust Architecture, organizations need to ensure that remote network traffic is encrypted, and only authorized users are granted access. It is crucial to have a VPN or specified network access protocols set up to reduce chances of sensitive data leaks.
Here are some key measures to secure network access:
- Use Virtual Private Network (VPN) or Zero Trust Network Access (ZTNA) solutions
VPNs and ZTNAs provide secure remote access to your organization’s network. VPNs create an encrypted tunnel for remote traffic, while ZTNAs use granular, role-based access controls based on user identity, device posture, and location. Both solutions can help protect against eavesdropping, man-in-the-middle attacks, and other network-based attacks, ensuring that remote network traffic is encrypted and secure. - Implement strict access controls
User identity can be verified through multi-factor authentication (MFA) and strong, unique passwords. Device posture checks can verify that remote devices meet security requirements, such as having up-to-date patches and antivirus software. Location-based access controls can restrict access from certain geographic regions or countries to minimize risk. These strict access controls ensure that only trusted users and devices are allowed access to your network. - Continuously monitor and analyze network traffic
Implement robust network monitoring and analysis tools to detect any signs of suspicious activity. Continuously monitoring network traffic allows for timely detection of potential security incidents, such as unusual traffic patterns, known malicious IP addresses, and abnormal user behavior. C.
These measures are essential in implementing a Zero Trust Architecture, where trust is not automatically granted based on location or network boundaries, but rather based on user identity, device posture, and other contextual factors, ensuring a higher level of security in remote environments.
4. Monitoring User Behavior
Remote users may access sensitive data and systems from various locations, making it essential to detect any anomalous behavior that could indicate a security breach. These measures can help detect and respond to potential security threats proactively, ensuring the security of sensitive data and systems in a Zero Trust Security Architecture.
- Implement User and Entity Behavior Analytics (UEBA): UEBA solutions use advanced analytics and machine learning algorithms to detect anomalous user behavior based on historical patterns and context.
- UEBA can help identify suspicious activities such as unusual login patterns, access to unauthorized resources, privilege escalation attempts, and data exfiltration attempts.
- Use security information and event management (SIEM) solutions: SIEM solutions can help centralize and analyze logs from various sources, including remote user activity logs.
- SIEM solutions can provide a holistic view of remote user activity and can detect patterns of behavior that may indicate security risks. By analyzing remote user logs, organizations can gain insights into user behavior and identify any potential security incidents that may require further investigation.
5. Educating Remote Users
In a zero trust security architecture, remote users play a critical role in maintaining the security of the network. It is important to educate remote employees on the risks associated with remote work and the best practices for maintaining secure access to company resources.
Provide Regular Security Awareness Training: Conduct regular security awareness training sessions for remote employees to educate them on best practices for remote work security. This can include topics such as password hygiene, phishing awareness, social engineering, safe browsing habits, and secure file sharing practices.
Educate Remote Users about Common Cyber Threats: Remote employees should be educated about the risks of common cyber threats, such as phishing attacks, social engineering attempts, malware, ransomware, and other types of attacks. They should be trained to recognize warning signs of these threats and know how to respond appropriately. Providing examples of real-world scenarios and practical tips can help remote employees make informed decisions and avoid falling victim to cyber attacks.
- Encourage Prompt Reporting of Security Incidents: Remote employees should be encouraged to report any security incidents or suspicious activities immediately to the IT or security team. This can include suspicious emails, unusual login attempts, or any other behavior that seems suspicious.
- Provide Clear and Concise Security Policies: Remote employees should be provided with clear and concise security policies that outline the organization’s expectations for remote work security. These policies should cover topics such as password requirements, acceptable use of company resources, data handling guidelines, and reporting procedures for security incidents.
Following the above recommendations helps create a culture of security awareness and accountability among remote employees, reducing the risk of security breaches in remote work scenarios.
6. Regular Auditing & Compliance
Implementing Zero Trust Architecture in remote work environments requires regular auditing and compliance monitoring to ensure that security controls are effectively implemented and maintained.
Conduct Regular Security Audits: Regular security audits should be performed to assess the effectiveness of the Zero Trust security controls in place for remote work environments. This can include reviewing access controls, user permissions, authentication mechanisms, and other security measures to identify any potential vulnerabilities or weaknesses. Audits should be conducted by qualified personnel with expertise in information security and compliance.
Review Compliance with Security Policies: Remote work environments should comply with the organization’s security policies and industry regulations. Regular reviews should be conducted to ensure that remote employees are adhering to established security policies, such as password requirements, data handling guidelines, and acceptable use of company resources. Any non-compliance issues should be addressed promptly to minimize security risks.
Ensure Compliance with Industry Regulations: Remote work environments must comply with relevant industry regulations and standards, such as GDPR, HIPAA, PCI-DSS, or others depending on the industry and location of the organization. Regular audits should be conducted to ensure compliance with these regulations and address any non-compliance issues.
Challenges of Implementing Zero Trust Security (ZTA) Architecture
As organizations embrace the paradigm shift towards Zero Trust Security, it is crucial to understand the challenges that may arise during the implementation and maintenance process, especially in remote work environments.
These challenges span across resource allocation, user experience considerations, compliance requirements, scalability, and vendor support. By being aware of these hurdles from the outset, organizations can proactively strategize and mitigate potential roadblocks, ensuring a successful implementation of Zero Trust Security.
- Resource Allocation: Allocating the necessary resources, such as budget, personnel, and infrastructure, for implementing and maintaining Zero Trust Security in remote work environments can be a challenge, especially for organizations with limited resources.
- User Experience Considerations: Balancing security measures with user experience can be challenging, as overly strict security protocols may hinder remote workers’ productivity and create friction in their workflow. Organizations need to find a balance between security and user experience to ensure smooth remote work operations.
- Implementation Complexity: Implementing Zero Trust Security requires integration of multiple security technologies and solutions, which can be complex and time-consuming. Organizations may face challenges in managing the complexity of implementing and maintaining a comprehensive Zero Trust Security framework.
- Change Management: Implementing Zero Trust Security involves significant changes in access controls, authentication processes, and other security protocols, which may require changes in user behavior and habits. Organizations may face challenges in managing the change and ensuring user adoption of the new security measures.
- Compliance and Regulatory Requirements: Organizations need to comply with various compliance and regulatory requirements, such as GDPR, HIPAA, and industry-specific regulations, while implementing Zero Trust Security in remote work environments. Ensuring compliance with these requirements can be challenging and may require additional efforts and resources.
- Vendor and Partner Management: Implementing Zero Trust Security may involve working with multiple vendors and partners for different security solutions, such as MFA, IAM, and network segmentation. Organizations may face challenges in coordinating and managing these vendors and partners to ensure interoperability and smooth operation of the Zero Trust Security framework.
- Monitoring and Incident Response: Organizations need to have effective monitoring and incident response capabilities in place to detect and respond to security incidents in a remote work environment. This may require investments in SIEM systems, security analytics tools, and trained security personnel to ensure timely detection and response to security events.
- Scalability and Flexibility: Scaling and adapting Zero Trust Security to different remote work scenarios, such as varying access requirements, diverse devices, and network environments, can be challenging. Organizations need to ensure that their Zero Trust Security implementation is flexible enough to adapt to changing requirements and scalable to accommodate growing numbers of remote workers or changing business needs.
- User Education and Awareness: Educating remote workers about the importance of Zero Trust Security protocols, such as strong authentication and access controls, can be a challenge. Organizations need to invest in user education and awareness programs to ensure that remote workers are knowledgeable and compliant with the security measures.
- Vendor Support and Interoperability: Ensuring vendor support and interoperability of different security tools and technologies in the Zero Trust Security implementation can be challenging. Organizations need to ensure that different security solutions work seamlessly together and are supported by the vendors to avoid any technical issues or disruptions.
How Caplock Security can Help
As organizations navigate the challenges of implementing Zero Trust Security in remote work, cloud services, and SaaS environments, Caplock Security provides a range of comprehensive services to help overcome these obstacles and protect critical assets and data from cyber threats.
How Caplock Security can Help:
- Assess & Define: Gain clarity on security posture, attack surface, and sensitive assets.
- Create Visibility: Map data flows, access requirements, and service accounts for vulnerability identification.
- Establish Preventative Measures: Implement multifactor authentication, least privilege, and micro-segmentation to deter hackers.
- Continuously Monitor: Detect and respond to anomalous activity with real-time network monitoring and log analysis.
- Zero Trust Assessment & Planning: Accelerate implementation with fast deployment, vendor-agnostic integration, and complete visibility.
- User-Friendly Solutions: Enjoy intuitive traffic control, policy management, and access monitoring through a single cloud-delivered portal.
- Actionable Intelligence: Leverage observation and learning for continuous policy optimization and actionable security insights.
If your organization wants to implement Zero Trust Security effectively and seamlessly, reach out today without hesitation, and get access to Caplock Security’s range of services.
Act on time to prevent potential security disasters and safeguard your critical assets and data from cyber threats. Don’t wait to be a victim of a cyberattack. Take preventative measures today.











Leave a Reply
You must be logged in to post a comment.