Protect Healthcare Data With These Cybersecurity Tips
Cyberattacks in Healthcare
The sophistication of cyberattacks has increased dramatically in the past ten years, along with cyberthreats to the healthcare industry. With each development brought about by automation, interoperability, and data analytics, the potential of malicious intrusions increases. Because they can directly compromise patient safety, health, and data security, cyberattacks are a significant concern for the healthcare sector.
Technology has become increasingly vital in managing patient and hospital relations at this time when healthcare institutions are already operating at full capacity. The most crucial factor to take into account within Health Management Information Systems (HMIS) is cybersecurity. Hospitals were able to develop a secure and safe synchronization method with the aid of healthcare IT systems.
Hackers’ strategies have quickly advanced in order to fraudulently exploit fear for ransom payments as a result of hospital inefficiencies during the pandemic. Particularly in the health care industry, adopting cyber security best practices has become essential for keeping up with growing threats. A large number of cybercrimes, including phishing attempts and hacks, have been recently reported.
Healthcare Cybersecurity Tips
These cybersecurity best practices for healthcare organizations are designed to keep up with the changing threat landscape, addressing risks to endpoint privacy and data protection as well as those in the cloud, and protecting data while it is in use, in transit, and at rest. A complex, multifaceted security strategy is necessary for this.
1) Limit Network and Infrastructure Access
Network Access Measures
Within small organizations, setting file access permissions may be done manually, using an access control list. Only those with appropriate access rights to the system are able to do this. It is crucial to decide which files should be accessible to which staff members before establishing these rights.
Users who have access should only be able to see the information necessary for their tasks, and access to sensitive and vital data should continue to be granted on a need-to-know basis. Additionally, it is essential to ensure that the administrator immediately terminates access when it is no longer required.
Visitors devices should not be allowed access to the network because it is improbable that their security can be properly verified in a timely manner. The greatest protection is to forbid casual access because it is costly and time-consuming to set up a network to safely permit guest access. Each authorized device must be identified to the router during wireless network configuration; only then can the device be granted access.
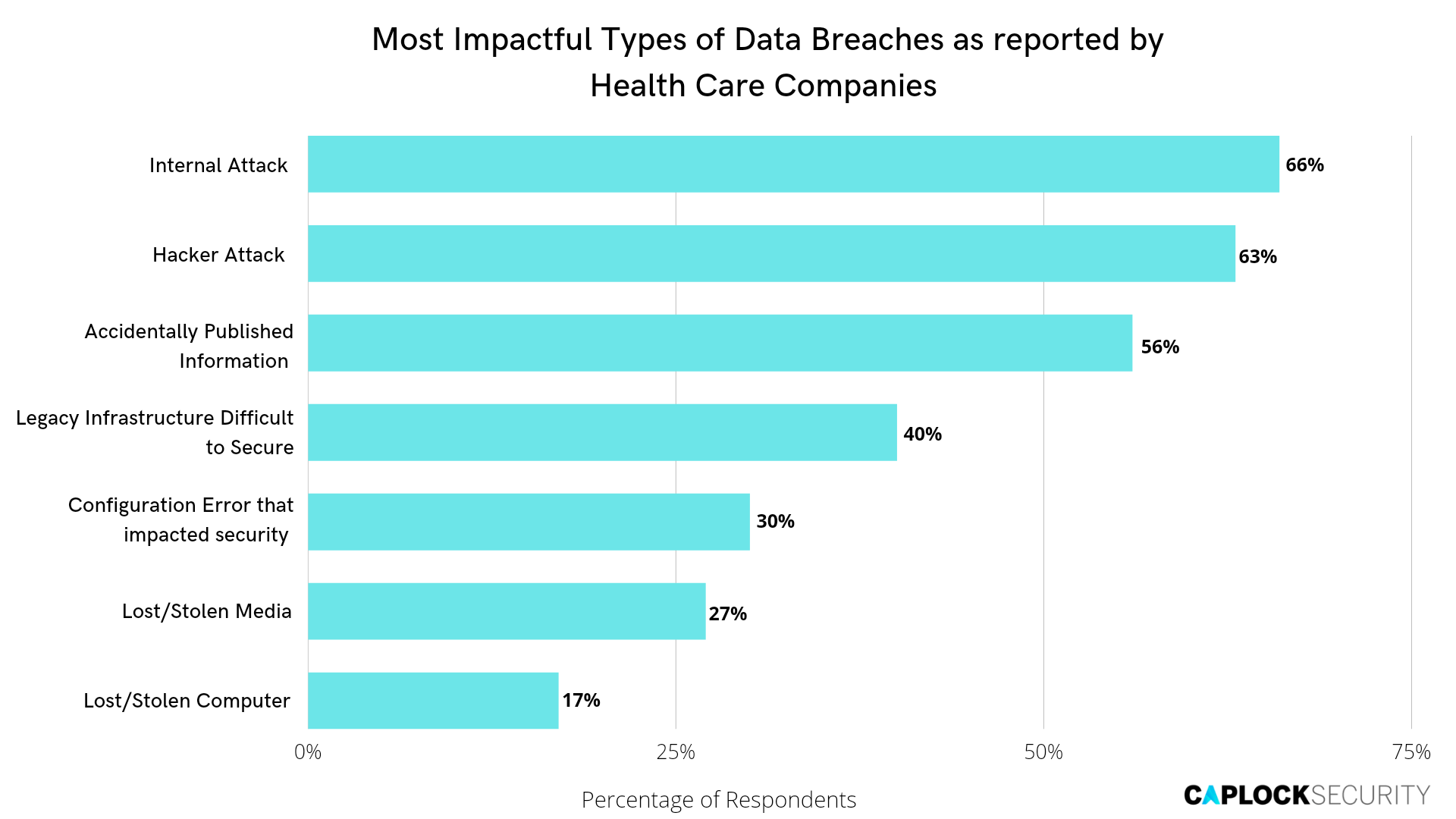
Physical Access Measures
Loss of devices is the most frequent method that electronic health information is compromised, either via theft or accident. According to incidents reported to the Office for Civil Rights, portable storage media accounts for more than half of all occurrences of data loss. The most common types of lost or stolen devices are listed below.
- Laptops
- Mobile devices
- Desktop computers
- Hard drives
- Backup tapes/drives
- Complete network servers
Policies restricting physical access should be part of the physical security of devices and data. Common examples include keeping actual credentials under lock and key, protecting machines in locked rooms, and limiting access to equipment in secure areas.
Two key variables should be taken into account when deciding where to host a server that houses electronic health information:
- Focus on physical security should be on preventing unauthorized individuals from accessing the server.
- The server should be shielded from the elements, such as fire, water, and other hazards.
2) Using Anti Virus
Viruses and similar code that exploit machine vulnerabilities are the primary means by which attackers compromise computers within smaller networks. As a result of the nature of the computing landscape, these vulnerabilities are common. Even if a computer has all of the most recent security updates for its operating system and applications, it may still be vulnerable due to previously undetected flaws. Furthermore, seemingly innocuous external sources such as CDs, email, flash drives, and web downloads can infect computers.
As a result, it is critical to use a product that provides constantly updated protection. Anti-virus software is widely available, has been proven to be reliable, and is reasonably priced.
To protect against the most recent computer viruses and malware, anti-virus software requires regular updates from the vendor. Most anti-virus software generates automatic reminders about these updates, and many are set up to allow for automated updating. Without anti-virus software, data can be stolen, destroyed, or defaced, and attackers can take advantage of this to command the machine.
3) Security Awareness Training
Human error remains one of the most serious threats to security in all industries, but especially in healthcare. Human negligence can have disastrous and costly consequences for healthcare organizations. Security awareness training provides healthcare employees with the knowledge they need to make wise decisions and exercise appropriate caution when handling patient data.
The user is frequently the weakest link in your cyber-security practices. Training employees on how to protect your data is critical, as is enforcing these measures, and education should be ongoing. Uninstall any unnecessary software and encourage employees to avoid downloading any, as well as disable file-sharing and remote printing to avoid accidental data sharing with unauthorized personnel.
Configuration Management
New computers and software packages come with a bewildering array of options and little guidance on how to configure them to ensure system security. In the face of this complication, it can be difficult to know which options to enable and which to disable. Listed below are some generally good cybersecurity based configuration changes that can be implemented for added protection.
- Uninstall any software application that is not essential to running the practice (games,
instant message clients, photo-sharing tools, etc.)
- Do not simply accept defaults or “standard” configurations when installing software. Step through each option, understand the choices, and obtain technical assistance where necessary.
- Find out whether the device vendor maintains an open connection to the installed software (“back door”) in order to provide updates and support. If so, ensure a secure connection at the firewall and request that this access be disabled when not in use.
- Disable remote file sharing and remote printing within the operating system configuration.
Allowing these could result in the accidental sharing or printing of files to locations where
unauthorized individuals could access them.
Importance of Logging
The logging of all access and usage data is essential since it allows service providers and business partners to keep track of which specific users are gaining access to data, programs, and other resources. These logs are useful for audits, assisting firms in locating problem areas and, if necessary, stepping up security. When an incident occurs, an audit trail may help businesses identify the exact access points, ascertain the reason why, and assess the damage.
4) Strong Password Strategy
Passwords are the first line of defense against unauthorized computer access. A password should be required to log in, regardless of the type or operating system. A strong password will not stop attackers from attempting to gain access, but it will slow them down and discourage them.
Passwords that are difficult to guess are considered strong. Because attackers may use automated methods to guess a password, it is critical to select a password that lacks characteristics that could make it vulnerable.
Strong passwords should not contain the following:
- Words from the dictionary, even if slightly altered (for example, replacing a letter with
a figure) - Personal information such as birth date, names of self, family members, or pets, social security number, or any other information that others could easily learn.
- Never use a piece of information from a social networking site as a password.
Some examples of strong password characteristics are as follows:
- A minimum of eight characters (the longer the better).
- A mix of upper and lower case letters, one number, and at least one special character
a distinguishing feature, such as a punctuation mark.
Finally, systems should be set up to require password changes on a regular basis. While this may be inconvenient for users, it also reduces the likelihood that a system will be easily hacked.
Multi-factor Authentication
Multi-factor Authentication (MFA) is a type of authentication that is used when a user logs into a system. To gain access to the system or an application, the user must provide two or more verification methods. It has been shown to reduce the likelihood of a cyberattack by providing multiple layers of protection rather than relying solely on a username and password for authentication. When used alone, weak and easily predicted passwords can be easily hacked.
5) Backup and Recovery
From the first day a new EHR is operational in a practice, the data must be regularly and consistently backed up.
Because a backup is one that can be relied on in an emergency, it is critical that not only is all data correctly captured, but that it can be restored quickly and accurately. Backup media must be tested on a regular basis to ensure that they can be properly restored.
Critical files can be manually copied onto backup media, but this can be time-consuming and error-prone. If at all possible, use an automated backup method. Some backup media, such as magnetic tape and removable hard drives, are reusable. These media devices can deteriorate over time and after repeated backup cycles. As they age, it is especially important to test them for reliable restoration operations.
Recovery planning must be done so that when an emergency arises, there is a defined method in place. In the event of a crisis, health care practitioners may be called upon to provide medical records and information as soon as feasible. The organization must be prepared to access backups and restore capabilities, which necessitates knowledge of what data was backed up, when the backups were performed (timeframe and frequency), where the backups are kept, and what equipment is required to recover them. If feasible, this information should be kept in a remote location where someone is responsible for producing it in an emergency.
Conclusion
Healthcare organizations and professionals should make cybersecurity their top priority. It is crucial that entities make sure that sensitive data is effectively protected and secured in an era where cybersecurity risks result in significant losses and lawsuits across all industries every year.
Outsourcing cybersecurity services and utilizing modern protection and monitoring technologies will assist in ensuring that your healthcare security plan is solid and that your customers’ data is secure, while freeing up your own personnel to focus on other business issues.
Our team at Caplock Security is made up of devoted security professionals with years of experience in a variety of cybersecurity fields. Several of our clients have already used our assistance to improve their security standards, compliance requirements, and lower their risk. Our professionals can assist you in locating your security vulnerabilities and offer advice on how to fix them effectively.