Spot Scams & Phishing with these 10 Email Security Essentials
The Importance of Email Security
Almost every business uses emails regularly, with the average employee receiving at least 90+ emails a day. Of these, almost 80% are spam, phishing attempts, and malware. In a time-constrained environment, employees have very little time to devote to inspecting and approving the right mail. This makes emails a very efficient gateway to your organization for cybercriminals.
We must also keep in mind that there is always a delay between sending and receiving an email. Once intercepted, information can be read on any device without decryption since it is in an open format. In fact, information passes through a number of networks and servers, some of which are unsecured and susceptible, before arriving in an inbox. Even if an individual’s computer is safe from an attacker, the network or server that the email must pass through might not be as reliable.
To secure users and their devices, an email security system with multiple layers of protection is essential. Email is almost always the primary method used by businesses to communicate with clients, partners, and suppliers, as well as among employees. Organizations become vulnerable to cyberattacks if email safety best practices aren’t implemented around this crucial communication channel.
One malicious email can have the following repercussions :
- Credential Theft
Phishing emails can be created with the intention of stealing an employee’s username and password. These credentials can be used to remotely access both local and cloud-based services in order to steal data or carry out other tasks. - Payment Fraud
Business Email Compromise (BEC) and related frauds pretend to be senior executives of an organization. Under the guise of finishing a deal or settling a vendor invoice, these emails direct an employee to deposit money into a specific account. - Trojan Setup
Many malicious emails contain a Trojan that aims to infiltrate the target computer. Then, this malicious software will gather information and perhaps download different kinds of malware, such as keyloggers or ransomware. - Delivery of ransomware
Phishing emails are one of the main ways that ransomware is distributed. On machines that have been infected, a ransomware assault encrypts all of the files and demands money to decrypt them. No assurance of a full recovery exists, even if the ransom is paid.
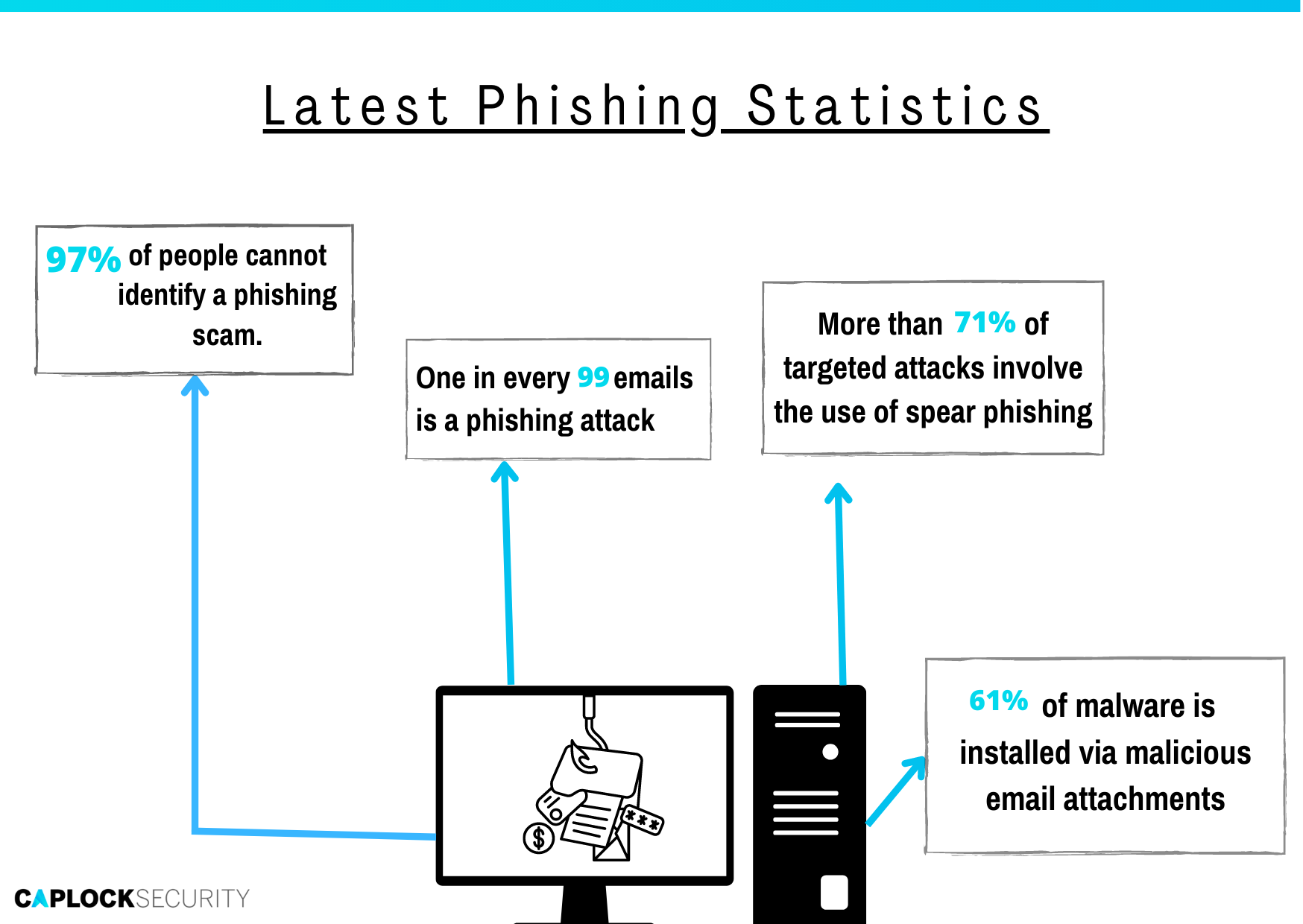
Email security is more important than ever as cybercriminals develop more powerful attack tactics and sophisticated approaches. Organizations today have more network connections, allowing people to access resources and systems from different locations and new devices. They also need to secure new equipment like Internet-of-Things (IoT) devices as well as more web-based apps, money held in more online locations, social networking accounts, and more. Let’s take a look at some statistics and the most common types of email attacks.
Types of email attacks
To hack through email, cybercriminals employ a variety of strategies, some of which can seriously harm an organization’s data and/or reputation. Each of the following approaches can be used to install malware on a computer, which is malicious software that is used to damage or manipulate a device or its data.
Phishing
One of the largest security risks to businesses is phishing attacks. Cybercriminals use methods to deceive users into believing they are legitimate senders in an effort to obtain their account information, start fraudulent payments, or use email spoofing to fool them into visiting dangerous websites. Phishing emails frequently inform victims that they have a pressing problem that has to be resolved right away in messages that pretend to be from service providers like banks.
As cybercriminals have gotten more skilled and inventive with their methods, phishing efforts can take many different forms. These assaults are similar in that they all aim to commit identity theft or spread malware. The various phishing attack types are listed below.
- Spear Phishing
Spear phishing attacks target specific people in an organization, unlike broad email attacks, which send out hundreds of emails at once using spam-like techniques. Hackers use the target’s name, title, company phone number, and other details to customize their emails in this type of fraud, leading the recipient to believe that the sender is familiar with them personally or professionally. - Whaling
A spear phishing variation called whaling targets CEOs and other executives (“whales”). The risk-reward ratio is significantly higher because these people frequently have unrestricted access to confidential corporate information. Whaling is for criminal organizations with the resources to carry out this type of cyberattack. - BEC (Business Email Compromise)
Business email compromise, or BEC, assaults are intended to pose as senior executives in order to deceive staff members into sending money for goods or services to fictitious bank accounts. The most harmful and successful form of cybercrime in 2019 was BEC fraud. - Clone phishing
In this kind of assault, the scammer makes a nearly exact replica of an official email, like an alert they may get from their bank, in an effort to deceive the victim into disclosing sensitive information. The attacker replaces a link or attachment in the original email that seems to be genuine with a malicious one. The email is frequently sent from an address that seems similar to one of the original senders, making it more difficult to identify. - Vishing
Vishing, a form of voice phishing, is when a con artist impersonates the legitimate caller ID of a well-known, reputable business, such as a bank or the IRS, in an effort to get the target to pick up the phone. The con artist then assumes the identity of a manager or authority figure and employs blackmail or intimidation techniques to demand payment of money allegedly owing to that company. Vishing can also involve leaving voicemails for victims asking them to call back a number, and when they do, they are fooled into providing their personal information or account information. - Snowshoeing
Attackers try to get around standard email spam filters in a sophisticated method. They achieve this by sending out messages through numerous domains and IP addresses in such small quantities that reputation-or volume-based spam filtering algorithms are unable to immediately identify and stop fraudulent messages. Some of the communications reach inboxes before the filters figure out how to block them. This method is known as snowshoeing.
Spam
Since social networking and e-commerce platforms have become more popular, spam emails have increased. The “latest news” or announcements made by businesses are typically sent by email to a big audience of subscribers.
Spamming, has the potential to be catastrophic for businesses, if not the users, with the right kind of well-planned attack. Unwanted emails can be sent to even more people if a hacker manages to take over an organization’s email system.
Even worse, because the emails are being sent from valid email accounts, hackers might take advantage of the situation and send emails that include a virus or a phishing attack, infecting a lot of recipients.
Identity and Information Theft
Today, many businesses handle their email systems using services like Zoho, G Suite, Microsoft Office 365, or equivalent ones. In addition to hosting emails, services like this provide a variety of helpful business tools to handle information in one location. End customers do not require a separate set of login credentials to access them because they are all a part of the same suite as the email service.
When a hacker succeeds in stealing a user’s identity, companies tend to experience the same drawbacks whether they employ third-party security services or their own security methods (i.e., login credentials).
Employees typically use the suite to store confidential or sensitive information that will soon be made public if an attacker manages to access the employee’s email account. Identity theft via email now has considerably more serious repercussions than it did in the past.
Virus Attacks
Another way to use email as a vector is to launch a virus attack. It takes precise preparation to create and implement a virus, so a group is more likely than an individual to come up with the idea and carry it through.
Even the most basic viruses will try to trick their victims into downloading an attachment. They are actually files that are disguising themselves as documents and, when executed, either take control of the host or have more adverse effects.
A targeted virus can have specific or multiple purposes. Regardless of that, email itself is rarely a target, merely the first stage of the attack. If the attack is successful, the virus could quickly spread across the network in a short time and have the ability to shut down the entire network.
Email Security Recommendations & Tips
Since there are a variety of different attack options within the umbrella of emails themselves, there are different ways to prepare and mitigate for each type. The most useful ones are listed below.
Malware protection
- Install antivirus software that checks files, networks, and websites for potentially harmful activities and prevents malware from being sent or downloaded to devices to safeguard users’ endpoints. Users can use antivirus software to assist them in eradicating any malware found on their devices as well as to stop them from accessing or downloading harmful links or attachments from emails.
- Thanks to endpoint protection technologies, organizations can keep an eye on every device that connects to their network. When potentially harmful behavior is discovered, they can execute system scans that monitor access and usage across the network, which can send out alarms and stop traffic. This is crucial when employees are working from home or remote places and accessing business systems.
Data leakage & breach prevention
- Prevention of breaches and data leaking is the main goal of email security best practices. Employing certain procedures such as employee training, setting up email security measures, and urging users to use 2FA (Two Factor Authentication) and secure their passwords can stop attackers from focusing on specific individuals and exploiting flaws.
- Employees should use solutions like virtual private networks (VPNs) that encrypt their browsing sessions in addition to avoiding additional security concerns like accessing open or public Wi-Fi networks.
Email Encryption
- Solutions for email encryption are ideal for businesses with in-house email servers. Sending unsecured email communications puts any company that transfers sensitive data at a high risk of a cyberattack or data breach. Therefore, it is significantly more cost-effective to pay for an email encryption service to secure email than to risk the potential financial and reputational harm brought on by a breach.
- The most secure email encryption possible must be used by organizations that handle extremely sensitive data or are subject to strict regulatory compliance criteria in order to safeguard their incoming and outgoing communications.
Zero Trust Policy
Zero trust security is the process of eliminating points of vulnerability by limiting network access for users, as well as adopting extensive identity verification so that they only have access to the data and systems relevant to their position. The three steps necessary for implementing Zero Trust security are listed below.
- Continuous Monitoring Through Device Visibility and Micro Segmentation
- Multi-Factor Authentication and Identity-Based Access
- Endpoint Protection for On and Off-Network Devices
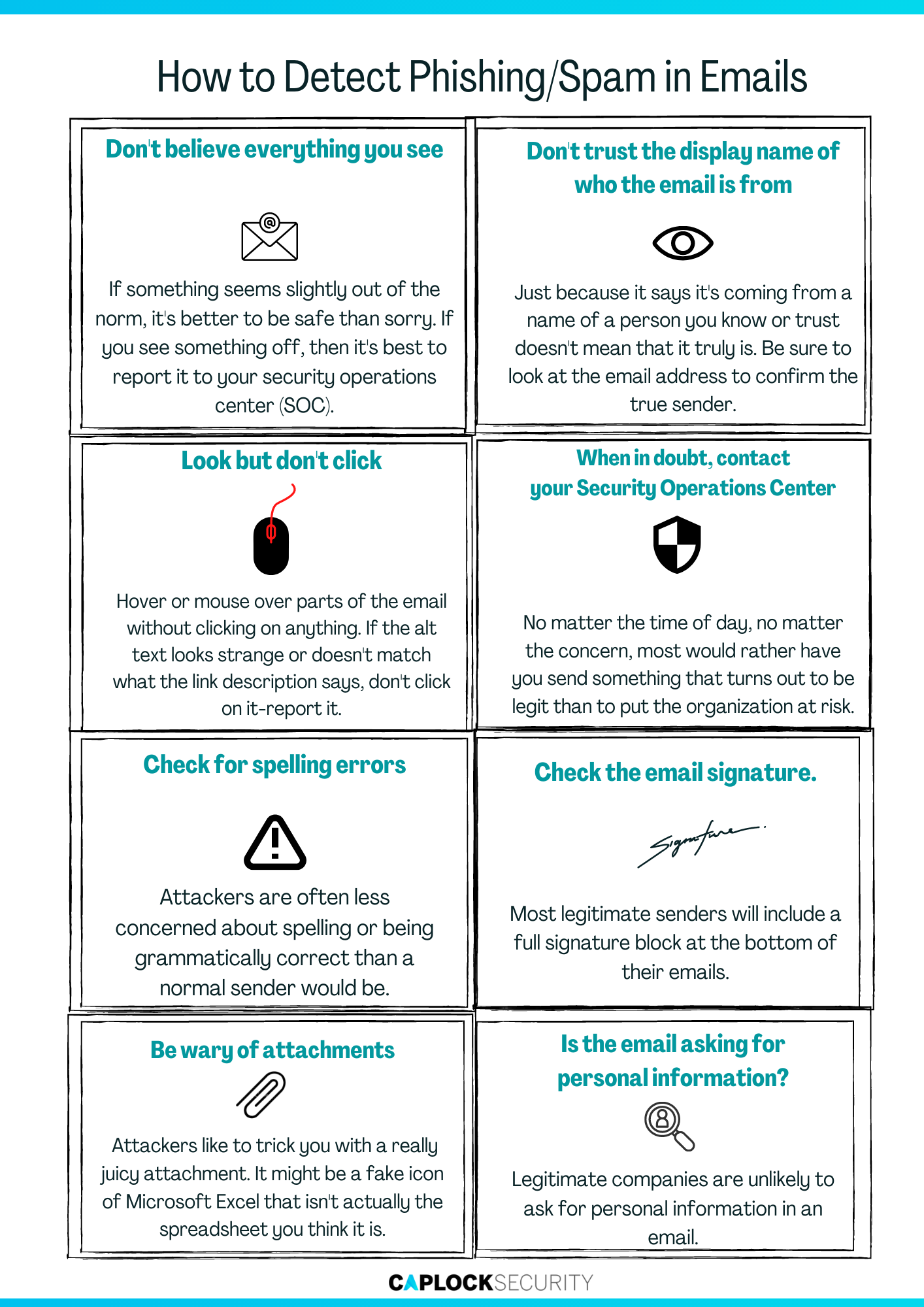
Employee Awareness
- The first line of defense against email-borne assaults is an organization’s workforce. Employees who have received cybersecurity awareness training are better informed about the risks they encounter, which lowers the organization’s cyber risk and enhances the likelihood that their data will remain secure. Make sure staff members are aware of potential attack indicators and the repercussions of disregarding email security best practices.
- A good company email security strategy must include employee education and security awareness training. Although CIOs, administrators, and IT experts are aware of the value of sensitive data, the necessity of corporate email security, and the repercussions of a successful phishing attack or breach, it is vital that workers be as well. The bulk of insider breaches are caused by human error or carelessness, and businesses can reduce this risk by teaching staff about their principles and values. The greatest way to reduce the risk of human error and enhance this vital defense is to regularly provide employees with comprehensive security training.
- Companies must educate their personnel about the characteristics of harmful emails and the value of not opening emails from unknown or unauthorized senders. Additionally, they must conduct courses on the quality standards for email attachment security and phishing email simulation.
Conclusion
Due to the various threats that are circulating via email, including malware, spam, phishing, and BEC, businesses shouldn’t rely solely on their email providers’ default security settings to protect their data. Even if G Suite, Office 365, and other email services have their own security measures, spending money on an advanced email protection solution will provide greater security and effectiveness. By doing this, the business avoids data breaches, malware attacks, and even issues brought on by data protection laws and regulations.
You should act right away to protect your company’s crucial operations in accordance with your business continuity plan. Businesses should test their backup procedures, disaster recovery procedures, and contingency planning strategies on a regular basis.
Prevention is superior to cure. Avoid the costly mistake of neglecting your organization’s cybersecurity aspect. Caplock Security gives you all the tools you need to streamline your security deployment without sacrificing performance, allowing for a unified strategy for efficient operations and getting you ready to scale for corporate expansion.