The Healthcare Industry’s Biggest Cybersecurity Vulnerabilities (2022)
Cybersecurity in Healthcare
Cyberthreats to the healthcare sector have grown significantly in the past ten years, along with the sophistication of cyberattacks. The risk of malevolent cyberattacks grows with each advancement brought about by automation, interoperability, and data analytics. Cyberattacks are a particular worry for the healthcare industry because they can directly endanger patient safety and health, in addition to system and data security.
The Health Insurance Portability and Accountability Act (HIPAA) regulations, the ethical obligation to assist patients, and the potential harm that healthcare security breaches can do to patients’ lives all require IT professionals to continuously address healthcare data security vulnerabilities.
Hospital network security is a major IT concern since electronic health records, or EHRs, contain a multitude of sensitive data about patients’ medical history. EHRs allow doctors, other healthcare professionals, insurance companies, and other parties to exchange crucial data. This facilitates insurance matters and makes it simpler to improve coordination.
Modern healthcare is networked, which poses concerns for IT security as it gathers so much vital information in one area that almost everyone uses, making it an obvious target for hackers and cybercriminals. In reality, there has never been a greater pressing need for data security in the healthcare industry. The need for medical organizations to develop precautions against Internet threats is greater than ever, which is why it’s critical to have a thorough grasp of the dangers and possible safeguards.
The Vulnerability of Healthcare Information Systems
Shared medical information has the paradoxical effect of making patients safer while also putting them at risk. Although the network’s data becomes more valuable as it grows in size for delivering high-quality medical care, it also becomes more appealing to cybercriminals.
Vulnerabilities are often sought after by hackers for the following reasons:
- Medical provider networks may include useful financial data in addition to a patient’s records.
- Nearly every individual’s personal information is accessible in some way, since there are very few people that do not interact with healthcare providers.
- Hackers can access the data that has been accumulated over many years under the names of patients, as EHRs are interconnected. Patient information exchange is essential to provide patients the best care possible, but it also makes networks very desirable targets.
Healthcare institutions have experienced more direct assaults in varying situations. Once a hacker has gained access to a network, they can install ransomware to encrypt files or disable vital services until the company pays a predetermined ransom. Organizations frequently have no alternative but to pay the ransom and hope that the money can eventually be retrieved since the healthcare industry is time-sensitive.
Network-linked devices can also be tricked into giving the wrong treatments or otherwise altering a machine’s operation, though this is less common. A hacker could potentially use this access for terrorism or to hold a healthcare provider for ransom, endangering the safety of individuals. Healthcare providers cannot afford these potential risks in medical settings where the difference between life and death is the change of a decimal or a small change in dosage.
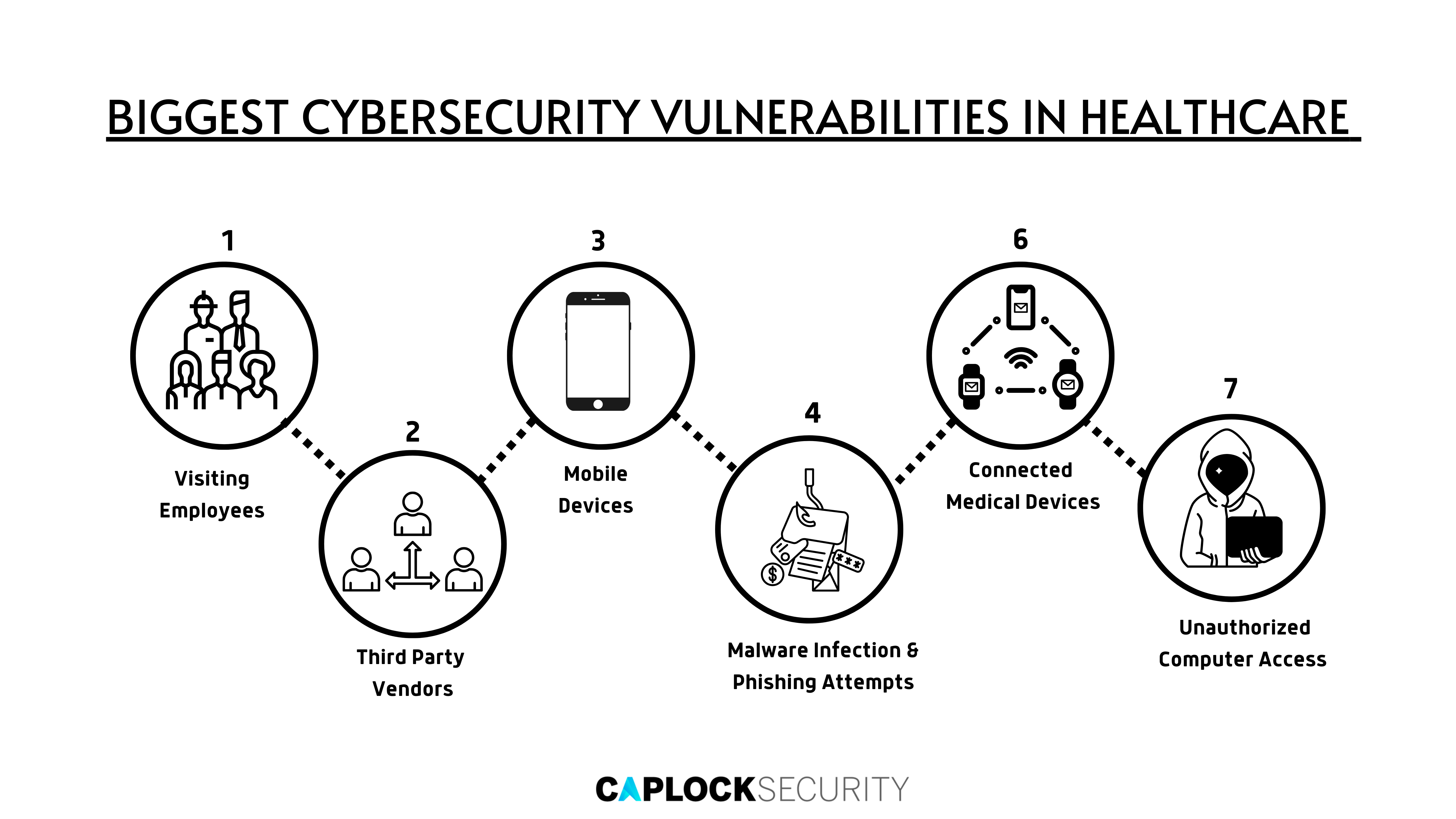
Biggest Cybersecurity Vulnerabilities in Healthcare
1. Visiting Employees
Patient files are readily available to staff members. While most people won’t abuse this authority, there is no certainty that others will not steal private data. This kind of information can be used by criminals to steal identities, but it can also be used to intimidate or even extort people. The theft of records by workers is a common occurrence. Employees occasionally gain access to private financial records and make a number of fraudulent purchases using patients’ credit card information. It has been discovered that other employees sometimes take face papers, which contain demographic and social security data that can be used to perpetrate a number of crimes.
The healthcare sector employs thousands of people to manage intricate computer systems, gather personal information, and handle vast volumes of confidential data. Breaches, errors, and password compromises are fairly common because of the size of the sector and the sheer number of people who have access to restricted systems and sensitive information. Cybercriminals will almost certainly succeed in their phishing attempts by tricking at least one network user, which is all it takes for today’s hackers to gain access to your systems.
2. Third-Party Vendors
Healthcare providers frequently collaborate with vendors without considering the risk involved. For instance, if a hospital contracts a cleaning service, the staff members may have access to computers. Although patient information should be secured such that even an ordinary employee cannot access it, which can be challenging to protect all avenues of access. Upkeep and cleaning are also crucial to preserving a safe working environment.
3. Mobile Devices
When allowing mobile logins, healthcare facilities don’t always demand that the devices adhere to security norms. Since staff communication devices are unaffected by the organization’s planning and security, this makes their networks susceptible to malware and hackers. When staff disposes of the equipment during an upgrade, the situation becomes worse because network information or passwords may still be available, providing a convenient entry point for crooks. Employers have few options unless the organization imposes stringent rules or outright prohibits user devices.
In a similar vein, lost or stolen electronics pose a serious threat. Any mobile device that is used to access the network of a facility becomes a liability the moment it is lost or taken. Once in the wrong hands, the user can quickly get into the system using previously used or saved login information. It can be difficult to identify an intruder or seal the breach once they’ve gained access to the network.
4. Malware Infection & Phishing Attempts
An entire system can be compromised by sophisticated malware and phishing attacks that install dangerous scripts on a computer or collect login information. The fact that malware can infiltrate your network with just one seemingly-authentic connection makes it one of the trickiest problems to deal with. It’s crucial to teach employees how to spot typical phishing scams. One classic scam involves emails from websites that appear legitimate asking for login credentials, something real businesses never do. The hacker on the other end can log in to the system as soon as a user enters such information. Various virus variants will collect information about records and immediately send it back to the original host or leave a backdoor entrance available for subsequent usage.
5. Connected Medical Devices
Online medical devices frequently lack adequate protection, making them attractive targets for hackers. There was a period when devices like infusion pumps only informed the patient and doctor who were using them. However, as the Internet of Medical Things (IoMT) develops, these gadgets are intended to interact with people outside of the doctor’s office and export data to external sources. There could be a variety of problems if this data was intercepted or altered. Additionally, hackers might get access to control the majority of network-connected devices, including how the machines operate.
6. Unauthorized Computer Access
Unauthorized personnel can readily access computers that are not in restricted areas. Unauthorized personnel or visitors could easily obtain damaging information if these open laptops are linked to sensitive patient data. In other instances, successful phishing attempts on PCs with open access provide hackers access to more delicate parts of the network. Ensure that any computer housing patient data is situated in a secure area.
7. Device Disposal
It’s common to think that after data has been destroyed, security concerns are resolved. However, the information is easily accessible to criminals when users incorrectly discard hard drives, outdated terminals, and other hardware needed to access a network with EHRs or credentials. Since this information can be recovered even after drives have been wiped or even reformatted, anything the user saved is still at risk.
Healthcare Security Precautions for Employees
The cyber protection effort is not limited to the healthcare sector. For years, small businesses have been searching for solutions to cybersecurity problems. One of the best approaches is to have every employee involved in maintaining the network’s security. Technology will continue to advance specific assaults and defenses, but there are broad staff policies that can dissuade cybercriminals.
Here are a few helpful practices that boost security precautions:
- Employee Awareness Training and Education
It is possible to establish an environment where security is valued and respected by assisting personnel to understand their part in cybersecurity and how it may affect patients’ lives. The emphasis the organization is placing on cyber safety is reiterated through regular briefings and communication on the state of the organization’s security. This message could also be emphasized by participating in employee training sessions and making cybersecurity a regular meeting topic. - Mandatory Software Updates
Cybercriminals frequently exploit security flaws in out-of-date software or other unprotected access points. Forcing software upgrades on devices, making use of two-factor authentication, and automatically implementing monthly password updates that demand “strong” password qualities are all ways to counteract this. By regularly setting corporate computers to periodically demand such changes, you can assist your staff by removing the need for them to create new passwords or click “allow updates” on each occasion. Again, this can be very challenging to enforce on employees’ own devices; therefore, training staff members on the value of updating is essential. - Established Procedures
Make a plan that outlines particular procedures for handling data and networks, both real and virtual, and make sure that these procedures are followed. The procedure becomes standardized when the expectations are made clear, enabling network security monitors to have more thorough control over the process. In addition to discouraging careless behavior that could jeopardize your ability to remain in compliance with HIPAA, developing suitable sanctions for failure to follow the processes emphasizes the importance you place on maintaining patient information security. - Personal Device Regulations
The use of mobile devices and the destruction of hardware that once held private data should be governed by tight rules established by healthcare organizations. Your IT managers can secure, control, and enforce policies on tablets, smartphones, and other devices using mobile device management (MDM) software, ensuring that employees don’t violate important policies and your data is kept secure.
Conclusion
Network security can appear to be a daunting, if not impossible, undertaking. Not only must all options be taken into account when creating a strategy, but you also need to figure out how to perform extensive maintenance to prevent systems from being vulnerable to the most recent hacking techniques and to comply with updated rules.
Despite these challenges, networked networks of patient data will keep expanding and absorbing more of the medical industry. Network security is a top priority for any healthcare firm because the consequences of information theft are too severe to take a chance on when considering a patient’s safety.
Our team at Caplock Security is made up of devoted security professionals with years of experience in a variety of cybersecurity fields. Several of our clients have already used our assistance to improve their security standards, compliance requirements, and lower their risk. Our professionals can assist you in locating your security vulnerabilities and offer advice on how to fix them effectively, by conducting the following essential activities.
- Medical Device Penetration Testing
- Network Segmentation for Medical Equipment
- Device Inventory and Risk Analysis
- Vulnerability Detection and Response
- Incident Monitoring and Response
- Medical Device Risk Assessments
- Vendor Risk Management and Reviews
- HIPAA Penetration Testing Services
Prevention is superior to cure. Avoid the costly mistake of neglecting your organization’s cybersecurity aspect. Caplock Security gives you all the tools you need to streamline your security deployment without sacrificing performance, allowing for a unified strategy for efficient operations and getting you ready to scale for corporate expansion.