What is Ransomware? – An Introduction
What is Ransomware?
Ransomware is a type of malware that encrypts files on a device, leaving those files and the systems that rely on them inoperable. Then, malicious actors demand a ransom in return for the decryption. Threatening to sell or reveal exfiltrated data or authentication credentials if the ransom is not paid is a common tactic used by ransomware perpetrators. The nation’s state, local, tribal, and critical infrastructure groups have seen an increase in ransomware outbreaks in recent years.
Ransomware can spread via malicious links and attachments in phishing emails, networks that are not setup securely, unintentionally accessing a website that is infected with malware, or installing a counterfeit software update. By using these steps, threat actors can enter the victim’s network, maneuver inside it, and eventually release the ransomware payload, opening the door for extortion. Following an infection, ransomware victims have three options: pay the ransom, attempt malware removal, or reset the device.
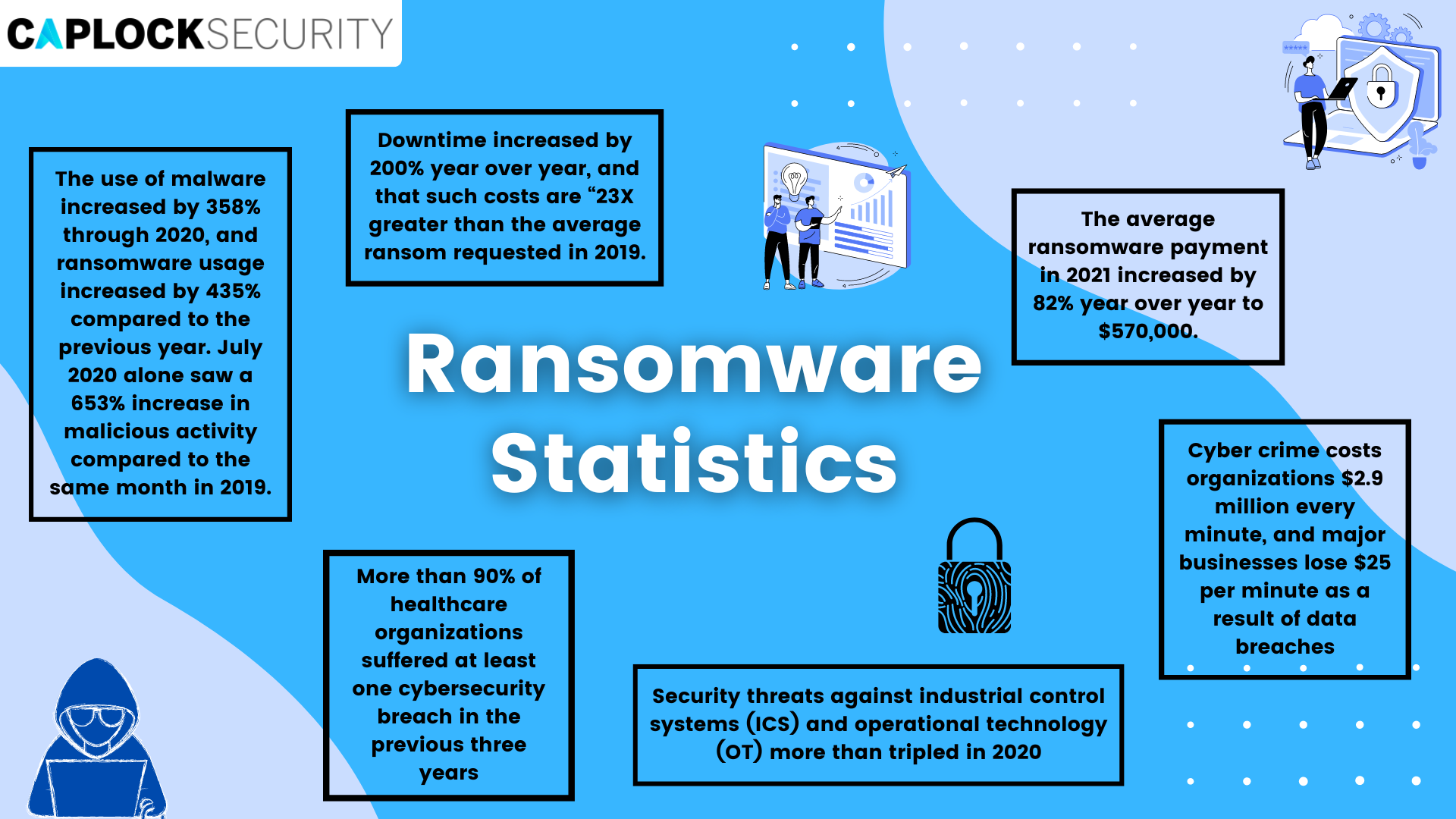
Ransomware poses a serious threat to both individual users and businesses in all forms and variations. Because of this, it is even more crucial to monitor the risk it carries and to be equipped for all possibilities. It is also important to educate yourself on ransomware, practice caution when dealing with sensitive data, and ensure you implement the latest preventative cybersecurity measures.
Types of Ransomware
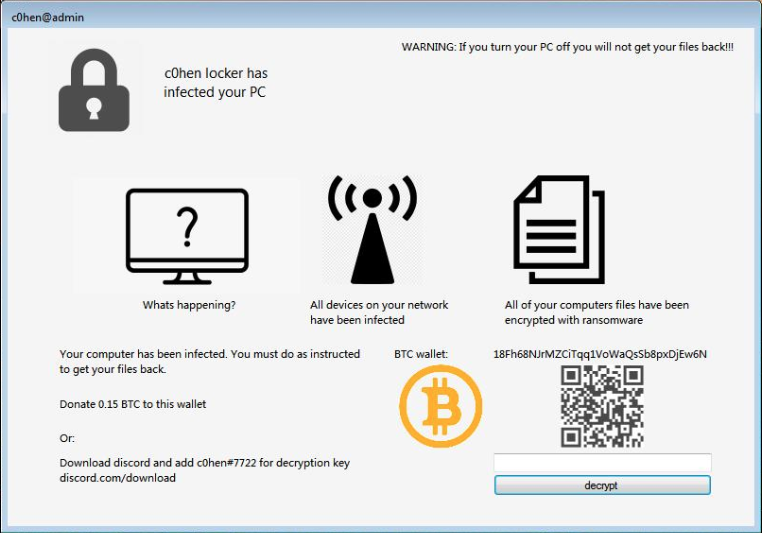
1. Locker Ransomware
This type of ransomware locks users out of their computers. Users are frequently only permitted to access the lock screen or interact with a window that displays the ransom demand. To pay the attacker, the mouse and keyboard would be partially enabled. An ominous timer with a deadline would be presented, to coerce users into paying up. Despite the timer, a positive aspect is that ‘Lockers’ typically just block users from accessing the data, not permanently destroy it.
2. Crypto Ransomware
The Crypto ransomware‘s objective is to encrypt your critical data, such as documents, images, and videos, but not to obstruct fundamental computer operations. The impact of crypto ransomware can be devastating due to the number of users who are unaware of the need for backups in the cloud or on external physical storage devices. Crypto developers frequently include a countdown to their ransom payment, with a message like: “If you don’t pay the ransom by the deadline, all your files will be deleted.” As a response, many victims just pay the ransom to regain access to their important files.

3. Leakware Ransomware
By using Leakware, the attacker threatens to reveal the data on public domains rather than erasing it. Attacks on institutions handling sensitive or confidential data, such as banks and government corporations, are also referred to as “Leakware” or “Doxware” attacks. In such situations, the majority of individuals panic and pay the ransom to avoid private and sensitive information getting into the wrong hands and becoming public knowledge.
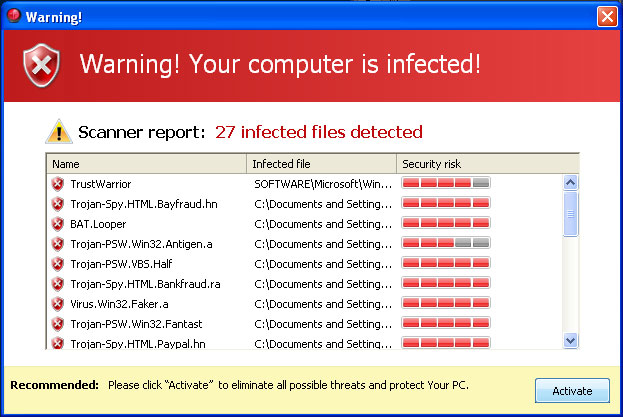
4. Scareware
By presenting an unsettling message, Scareware typically seeks to frighten users in order to deceive them into downloading malware. Attackers frequently entice victims to respond quickly without giving them much time to consider or examine their options by using prompts that appear authoritative and legitimate. The prompts may come in the form of a popup, an intimidating message, or a deceptive button that displays ominous text like: “Your computer is sluggish.” “Speed up Now,” or “Your IP can be seen by attackers; secure it immediately.” When users fall for the deception, the ransomware is able to enter their computers, lock them out, and encrypt their data.
5. Ransomware As a Service (RaaS)
RaaS is malware that is hosted anonymously by a “professional” hacker who manages all parts of the assault, from distributing ransomware to collecting funds and restoring access, in exchange for a cut of the money. RaaS functions as an affiliate network, enabling attackers with no technical expertise to sign up for it and conduct ransomware attacks. An affiliate’s members receive a cut of the ransom money. One of the main causes of the sharp rise in ransomware assaults in recent years is the RaaS model, which eliminates the requirement for prior coding expertise to launch an attack.
High-Profile Ransomware Attacks
Kaseya (2021)
Kaseya disclosed that its systems had been compromised on July 2, 2021. As a prime target, Kaseya, which offers IT solutions to other businesses, ended up having consequences for almost 1,500 organizations across several nations. According to a Reuters article, the cybercriminal group REvil claimed credit for the attack and sought ransom payments ranging from a few thousand to several million dollars.
REvil requested $70 million in bitcoin from Kaseya. Kaseya chose to work with the FBI and the US Cybersecurity and Infrastructure Agency rather than accept payment. On July 21, 2021, Kaseya acquired a global decryptor key and gave it to the affected organizations.
Colonial Pipeline (2021)
America’s biggest “refined products” pipeline was compromised with ransomware on May 7, 2021, by a hacker group known as Darkside. More than 100 million gallons of petroleum are transported daily along the 5,500-mile Colonial Pipeline. The attack had a substantial effect: as a result of vehicles rushing to the gas pumps in the days that followed, the average price of a gallon of gasoline in the US rose to more than $3 for the first time in seven years.
According to the pipeline operator, it used bitcoin to pay the hackers $4.4 million. The DOJ declared on June 7, 2021, that it had partially paid the ransom. Using a private key, US law enforcement authorities were able to track the payment and recover $2.3 million.
CNA Financial (2021)
CNA Financial, the seventh-largest commercial insurer in the US, announced on March 23, 2021, that it had “experienced a sophisticated cybersecurity attack.” A group by the name of Phoenix launched the attack, employing their Phoenix Locker ransomware. In May, CNA Financial finally paid $40 million to recover the data. While CNA has been discreet about the specifics of the deal and negotiations, it claims that all of its systems have subsequently been fully recovered.
Conclusion
Attacks using ransomware can take on a variety of forms and sizes. The attack vector has a significant impact on the kinds of ransomware that are employed. Always keep in mind what is at risk or what data could be erased or made public when estimating the scale and scope of the attack. Regardless of the ransomware kind, properly implementing cybersecurity measures and storing up data beforehand can considerably lessen the intensity of an attack.
You should act now to preserve your company’s critical operations in accordance with your business continuity plan. Businesses should keep backup plans, disaster recovery plans, and contingency planning procedures updated and test them periodically.
Prevention is better than cure. Do not make the costly mistake of ignoring the cybersecurity aspect of your organization. Caplock Security provides all the solutions needed to simplify your security implementation without impacting performance, provide a unified approach for streamlined operations, and enable you to scale for business growth.