Top 5 Cybersecurity Tools for Healthcare Organizations
Cybersecurity Tools in Healthcare
Big healthcare data has enormous potential for improving patient outcomes, predicting the onset of epidemics, collecting insightful knowledge, preventing preventable diseases, reducing healthcare delivery costs, and overall improving quality of life. However, it can be difficult to choose the correct data applications while preserving patient privacy and security rights.
Despite how critical big data is to the advancement of medical knowledge and to the success of all healthcare organizations, addressing security and privacy concerns is still necessary before big data can be implemented.
An organization can be protected from many forms of cybercrime and malicious attacks by using the correct cybersecurity solution. They can either be preventative or remedial. This means that they may either assist in landscape analysis to mitigate cyber risk or assist in better managing the risk once it develops as a vulnerability. It is recommended to use both types to achieve a balanced security posture.
Cybersecurity tools enable organizations to achieve the following objectives:
- Examine infrastructure data and IT setups to look for irregularities
- Automate processes for detecting and responding to incidents related to cybersecurity
- Recognize potential weaknesses from the perspective of a hacker
- Utilize security data that has previously been produced more effectively
- Develop web-based services and apps that are more secure
- In order to respond quickly, track user activity and network activity in real-time.
- Abide by compliance regulations and regulatory requirements
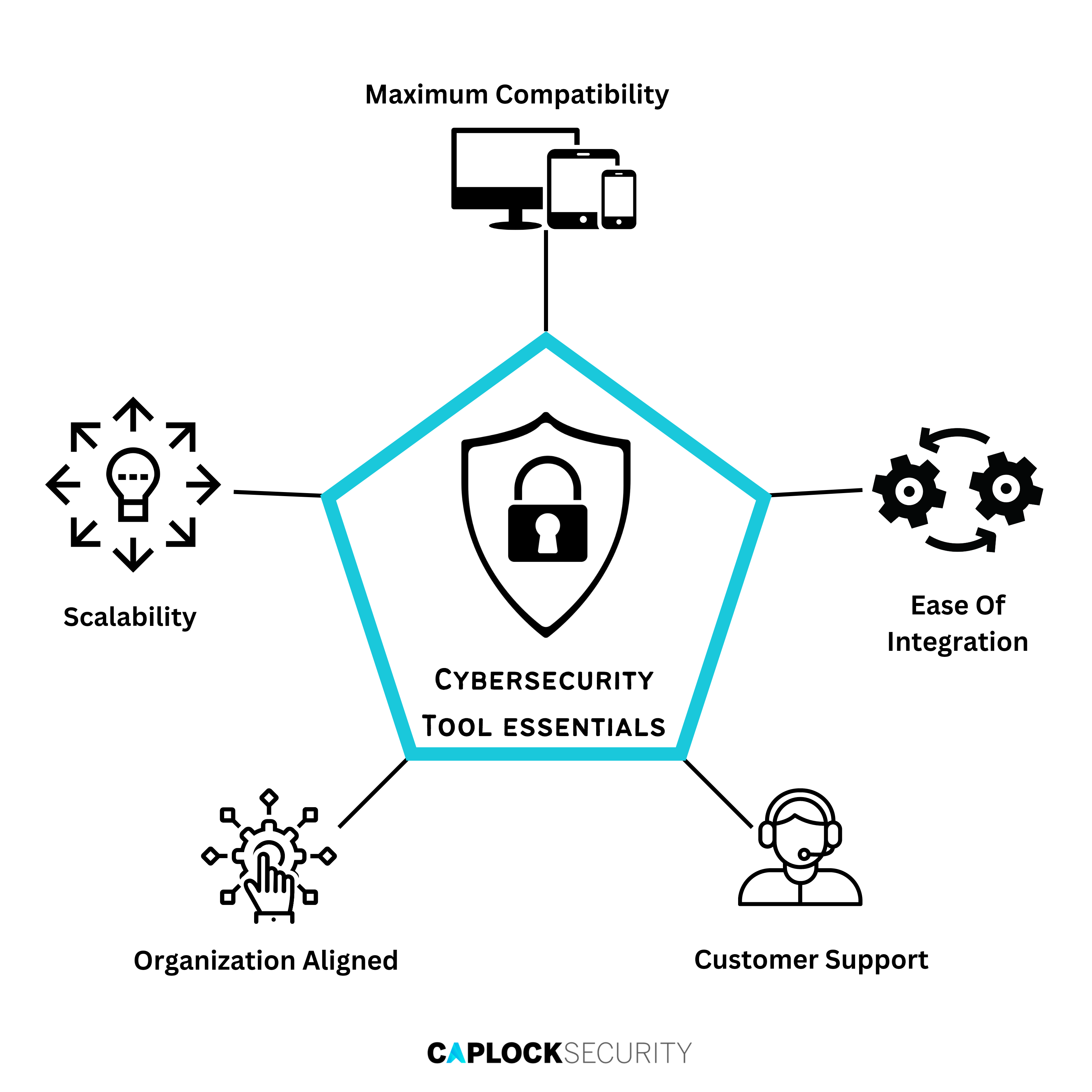
Crucial Elements of a Cybersecurity Tool
Scalability
The cybersecurity tool needs to be scalable for both volume and environmental variety. It should defend a large perimeter’s worth of endpoints and gadgets. As you expand, it should also support a variety of on-premises systems and cloud settings. Scalability is a crucial component, even for small-to medium-sized organizations, to ensure the tool’s viability in the long run.
Ease of Integration
In most cases, cybersecurity tools don’t work by themselves. For a seamless cybersecurity workflow free of fragmentation, they should interface with both upstream and downstream systems. All of your enterprise nodes, including the Internet of Things, should be connected to and fetched from the downstream side. It should be able to link to dashboards and alarm systems upstream. To accomplish this, the tool must have application programming interfaces (APIs).
Organization Aligned
Whatever use case you have in mind, the tool you select must be specially designed for it. For instance, you might desire an integrated identity-based security system or need a network activity analyzer. Malware protection may be desired by a small organization, while AI-driven security analysis may be desired by a major corporation. To successfully handle such events, cybersecurity technologies must be specifically designed.
Customer Support
Support is a key consideration when selecting any enterprise technology product, but it is especially important for cybersecurity technologies because the field is developing so quickly. Peer communities may provide assistance for open-source technologies, while large-scale commercial companies should ideally offer a premium support tier. Requesting professional assistance at the time of implementation is also a recommended option.
Maximum Compatibility
The cybersecurity instrument you choose must also work with your current and upcoming technological investments. It must be compatible with many device variations, operating systems, and cloud vendors. It must be able to run on-premises or in the cloud (as per your requirements). Tools that are based on open standards and have a vendor-neutral architecture are the most interoperable.
Top 5 Cybersecurity Tools for Healthcare Organizations
1) IBM QRadar
With an open, data-driven design, IBM QRadar is a tool for threat detection and response. It offers strong analytics and automation capabilities. Businesses that already produce significant amounts of security data can rely on IBM QRadar to improve their pro-active defense capabilities.
Key Features
- You can deploy QRadar XDR Connect, QRadar SIEM, QRadar NDR, etc. when your organization needs scalability to match your requirements.
- In order to facilitate integrations and prevent vendor lock-in, IBM QRadar actively employs open standards.
- To build a linked cybersecurity process, IBM QRadar was specifically designed based on AI-based analytics and intelligent automation.
- In addition to having an open architecture enabling out-of-the-box compatibility, QRadar also has IBM’s promise to customize the tool to meet organization needs.
The unique selling proposition about IBM QRadar is that it accelerates inquiry by 60x using proprietary AI technology. Since it contains advanced tools that require a good grasp of fundamentals, new users may find it difficult to segregate the overall picture from the specific event information due to the numerous protocols and regulations’ complex configuration requirements.
2) Kali Linux
Ethical hackers and experienced penetration testers frequently utilize Kali Linux, a Linux distribution, as a cybersecurity tool. It was introduced in 2013. A necessity for offensive cybersecurity strategies, Kali Linux is one of the most widely used cybersecurity tools for digital forensics. Utilizing a feature known as metapackages, Kali Linux can be individually modified. This enables IT specialists to finish information security jobs that demand time bound optimization efficiently.
Key Features
- It can grow across a variety of settings and devices, including virtual machines, Amazon Web Services (AWS), Docker containers, and mobile devices.
- Its open-source architecture makes it the best choice for integration.
- A U.S.-based business called Offensive Security developed it specifically for use cases in penetration testing and digital forensics.
- Along with receiving frequent updates, users can benefit from a large network of developers, ethical hackers, and information security specialists.
- A variety of graphical user interface (GUI) skins make Kali Linux adaptable to almost any scenario.
The unique selling proposition about Kali Linux is that it’s proven, effective, and free. It is also crucial to bear in mind that the tool is not intended for newbies; users must brush up on penetrating abilities peculiar to Kali Linux before beginning.
3) Bitdefender
Bitdefender GravityZone Advanced Business Security is a single platform that incorporates prevention, detection, response, reporting, and analytics. As a result, it serves as an all-inclusive solution for your cybersecurity requirements under a single license. Its product offers complete infrastructure protection for healthcare related IT sectors.
Key Features
- Depending on your infrastructure requirements, you can scale up after deploying several product modules or standalone solutions.
- It connects with a number of cybersecurity products offered by Bitdefender and by other third parties.
- Bitdefender offers both premium support options and robust managed service capabilities.
- It works with all endpoint variations, various network protocols, and multi-layered settings.
- With modules for Process Inspector, Network Defense, Web Threat Defense, and Antimalware, it is specifically created for commercial environments of all sizes.
Due to its modest initial investment, this solution is perfect for small-to-midsized organizations beginning their cybersecurity journey. Customers have complained that the user interface is slightly difficult to use and complicated, especially if you’re seeking analytics.
4) Malwarebytes
Malwarebytes provides a number of cutting-edge features, including role-based access, cloud-hosted sandboxes, and machine learning. As a result, it ranks as one of the most effective tools in this pricing niche. It offers powerful security tools for both commercial and residential use.
Key Features
- Malwarebytes may be scaled up or down to fit any scenario for needs of individuals, small, mid-sized, or large businesses.
- Through APIs, you can integrate it with the rest of your information security infrastructure.
- It is intended to offer industry-leading malware protection as well as endpoint detection and response capabilities.
- Customers have the option of choosing premium support plans and expert assistance for implementation and malware eradication.
- It is a fully functional utility that works in Chrome, Android, Windows, and Mac environments.
Malwarebytes can be trusted by rapidly expanding businesses as their needs increase from 1–9 devices to hundreds of endpoints and even servers. However, take into consideration that it lacks the ability to monitor behavior and occasionally may indicate a false negative.
5) Imperva Sonar
An analytics-based solution called Imperva Sonar automates the security of the edge infrastructure, data, and applications. It features a special behavioral analysis feature that tracks user behavior and notifies you when something seems off. It also offers trustworthy security for your content delivery network (CDN).
Key Features
- It collaborates with other IT and security products to provide coordinated workflows throughout the organization.
- Enterprise apps, cloud and on-premise data, and edge infrastructure, including APIs, are all protected by Sonar.
- Customers can benefit from thorough documentation, a peer network, and training via the Imperva University.
- Various endpoints, databases, application types, and network infrastructures are all compatible with this cybersecurity tool.
For application and data protection, there are individually priced plans available, as well as a free trial period. Companies that need to keep thorough security records for audits should use Imperva Sonar. It is also recommended to exercise caution in relation to false positives and insufficient support in particular geographic areas.
Conclusion
One of the leading initiatives for 2022 is enhancing cybersecurity within the healthcare industry. In order to conduct business, 81% of firms were compelled to circumvent cybersecurity protections, according to an EY survey. This means that in order to accommodate a world of remote and hybrid work, your cybersecurity posture needs to be significantly revised.
The five cybersecurity tools we covered assist in identifying and resolving vulnerabilities of all types so that a malicious entity has a very low chance of being exploited. These are the top tools that require enterprise attention as cybersecurity expenditure increases.
Our team at Caplock Security is made up of dedicated security professionals with years of experience in a variety of cybersecurity disciplines. Our assistance has already helped a number of our clients improve their security standards, comply with regulations, and lower their risk. Our specialists can assist you in locating your security flaws and can offer advice on how to successfully fix them.