5 Most Common Cloud Security Challenges & Solutions
Cloud Security: Addressing Challenges and Empowering Organizations
In the realm of cloud computing, the multitude of available services often poses a challenge for organizations to clearly demarcate their own responsibilities from those of their cloud service providers (CSPs), thereby exposing them to a multitude of vulnerabilities.
Furthermore, the expansive and far-reaching nature of the cloud amplifies the potential attack surface, necessitating the implementation of robust security measures to safeguard critical systems and sensitive data. It is evident that traditional security controls frequently fall short in meeting the distinctive security requirements posed by the cloud computing paradigm.
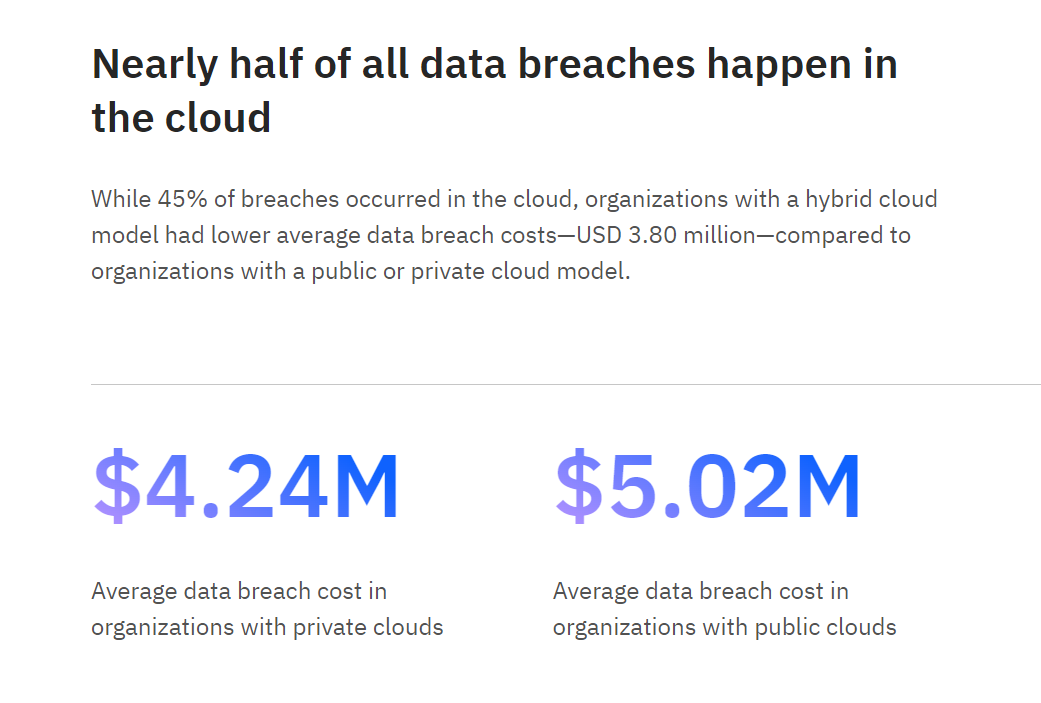
According to IBM’s annual data breach report, a staggering 45% of data breaches transpire in the cloud, underscoring the critical need for robust cloud security measures.
In this article, we explore the top 5 cloud security challenges faced by organizations and provide practical solutions to mitigate these risks effectively. Just as the allure of cloud computing lies in its advantages, it is essential to acknowledge and address the potential vulnerabilities that accompany it.
The Importance of Cloud Security
The rise in cyber threats and high-profile data breaches serves as a stark reminder of the critical importance of robust cloud security measures. Let’s take a closer look at some real-world examples of companies that suffered a cloud security compromise:
- Facebook: Over 530 million users’ personal data, including phone numbers, full names, and locations, was stolen and posted on a public database, leading to a tarnished reputation and regulatory scrutiny, resulting in a $5 billion penalty. (Source)
- Alibaba: A prolonged attack on Alibaba’s Chinese shopping website, Taobao, resulted in the compromise of over 1.1 billion pieces of user data, highlighting the need for better monitoring of systems and networks. (Source)
- LinkedIn: A data scraping breach exposed 700 million LinkedIn profiles, potentially providing ample information for social engineering attacks, emphasizing the data risks associated with using social media platforms. (Source)
- Accenture: Hackers from the LockBit ransomware group breached Accenture, stealing proprietary corporate data and compromising the company’s customers’ systems, underscoring the severity of cyber threats faced by organizations. (Source)
- Cognyte: Cyber analytics firm Cognyte’s failure to secure its database led to the exposure of 5 billion records containing names, email addresses, and data sources, emphasizing the need for comprehensive data protection measures. (Source)
In the following sections, we will embark on a deeper dive into the cloud security landscape, exploring the most common challenges organizations face and uncovering effective solutions to mitigate these risks effectively.
Security Challenges & Their Solutions in the Cloud Landscape
In this section, we will explore the most prevalent security challenges faced by organizations in the cloud and provide effective solutions to tackle these challenges head-on.
By understanding these challenges and implementing the recommended solutions, businesses can strengthen their cloud security framework and mitigate the risks associated with cloud computing.
Data Breaches & Lack of Control
Data breaches in the cloud landscape can have severe consequences for organizations, ranging from reputational damage to financial losses and legal liabilities.
One notable case illustrating the impact of misconfigurations in cloud infrastructure is the Capital One breach. This incident serves as a stark reminder of the critical importance of addressing the causes of data breaches in the cloud environment.
Causes of Data Breaches in the Cloud Environment
Misconfigured cloud settings or inadequate security controls
Improperly configured cloud resources, such as storage buckets, access permissions, or firewall rules, can inadvertently expose sensitive data to unauthorized access. Organizations should conduct regular audits of their cloud configurations, apply secure defaults, and leverage automation tools to ensure proper security controls.
Insider threats or malicious insider activities
Employees or individuals with privileged access may intentionally or unintentionally misuse their access privileges, leading to data breaches. Implementing strong user access controls, monitoring user activities, and conducting periodic security awareness training can help detect and mitigate insider threats effectively.
Vulnerabilities in cloud service provider (CSP) infrastructure or applications
Cloud service providers may occasionally have security vulnerabilities in their infrastructure or applications, which attackers can exploit to gain unauthorized access to customer data. To mitigate this risk, organizations should thoroughly assess the security capabilities and track record of their CSPs, ensure proper security controls are in place, and maintain open communication channels with the CSP for timely vulnerability remediation.

Solutions to Mitigate Data Breaches
- Implement strong access controls and authentication mechanisms
Enforce the principle of zero trust, granting users only the access they need, and use strong authentication methods such as multi-factor authentication to prevent unauthorized access to cloud resources. - Regularly update and patch cloud infrastructure and applications
Keep all cloud components, including virtual machines, containers, and software libraries, up to date with the latest security patches to address known vulnerabilities and reduce the risk of exploitation. - Employ robust encryption techniques to protect data at rest and in transit
Utilize strong encryption algorithms to protect sensitive data both when it is stored in the cloud and when it is transmitted over networks, preventing unauthorized access even if the data is compromised.
Lack of Cloud Security Architecture and Strategy
When it comes to the cloud, organizations often overlook the importance of a well-defined security architecture and strategy. Jumping into the cloud without careful planning can leave open holes for vulnerabilities and potential breaches.
To minimize risks, it’s crucial to understand the threats before taking the plunge. Ensure your team has cloud security expertise to guide the design of your cloud environment. Thoughtful migration techniques and strategies should be adopted to ensure a secure deployment.
Don’t forget to assess the security programs of your cloud service provider (CSP) and demand transparency. Look for third-party auditing and shared reports to gain confidence in your CSP’s security practices. Establish clear breach reporting terms to complement their technological solutions.
Introducing Cloud Security Posture Management (CSPM)
- CSPM solutions provide organizations with real-time visibility into their cloud environments, enabling them to identify and address misconfigurations, compliance gaps, and other security risks.
- By leveraging CSPM tools, organizations can proactively monitor their cloud infrastructure, detect potential vulnerabilities, and take prompt corrective actions.
- CSPM empowers businesses to enforce security best practices, maintain a strong security posture, and adhere to regulatory compliance requirements, ultimately enhancing the overall security and resilience of their cloud environments.
If your organization is planning to migrate or transfer to different cloud service provider, having a proactive consultation from a certified CSPM service provider will prove to be invaluable when building your Cloud Infrastructure.
Account Hijacking : Risks and Prevention
Cloud account hijacking poses a significant threat to the confidentiality, integrity, and availability of critical cloud environments. When a highly privileged and sensitive cloud account is compromised, the consequences can be severe, including data breaches and service disruptions.
Primary Causes of Cloud Account Hijacking
- Phishing Attacks – Cybercriminals employ phishing techniques to trick users into revealing their account credentials, allowing them to gain unauthorized access to cloud accounts.
- Weak or Stolen Credentials – The use of weak passwords or the reuse of passwords across multiple accounts increases the risk of account hijacking. Stolen credentials from data breaches on other platforms can also be leveraged to compromise cloud accounts.
- Third-Party API Installations – Installing third-party APIs without proper security measures and due diligence can introduce vulnerabilities that attackers can exploit to gain unauthorized access to cloud accounts. Insecure third party APIs are the number one reason for account hijacking.
- Improper Coding and Misconfigurations – Flaws in application code or misconfigurations in cloud settings can create vulnerabilities that enable attackers to exploit and compromise cloud accounts.
How do I ensure my third-party APIs are secure?
Integrating third-party APIs is common in the SaaS and cloud industry, but it’s crucial to prioritize their security to prevent account hijacking. Many hijacks occur due to unsecured APIs, so organizations must take proactive steps.
Start by thoroughly assessing vendors for their security practices and track record.
Follow API documentation and best practices provided by vendors, implementing secure API key management. Conduct regular security testing, including vulnerability assessments and code reviews.
Implement robust monitoring and incident response procedures to promptly address any suspicious activities. By prioritizing the security of third-party API installations, organizations can reduce the risk of account hijacking and maintain a secure cloud environment.
Limited Cloud Usage Visibility
Limited cloud usage visibility can have detrimental effects on organizations, leading to significant security challenges and concerns. The reason why this particular concern weighs heavy on leaders’
When enterprise admins have limited visibility into cloud usage, two critical challenges arise: unsanctioned app use (shadow IT) and sanctioned app misuse.
Unsanctioned App Use (Shadow IT)
Unsanctioned app use occurs when employees utilize applications that are not approved or permitted by the IT department. This can result in unmanaged and unsecured applications running within the organization, bypassing proper governance and security measures.
Sanctioned App Misuse
On the other hand, sanctioned app misuse refers to instances where approved applications are not used as intended. This can involve both authorized users using the app inappropriately and unauthorized individuals gaining access to the app using stolen credentials obtained through various means, such as SQL injection or DNS attacks.
Embracing the concept of shared responsibility
To address this challenge, both cloud service providers and customers have a shared responsibility. The Cloud Security Alliance (CSA) recommends developing a comprehensive cloud visibility effort from top to bottom within the organization. This includes mandating and enforcing companywide training on acceptable cloud usage policies to ensure employees understand and adhere to proper practices.
Why Partnering with a CSPM Provider is Right for Your Organization
For organizations looking to streamline their cloud security requirements and free up valuable time and resources, considering the services of a Cloud Security Posture Management (CSPM) provider is highly recommended. These managed security service providers offer proactive consulting and expertise in securing cloud infrastructure.
By partnering with a trusted CSPM provider before implementing their cloud environment, organizations can benefit from specialized guidance, comprehensive security assessments, and ongoing monitoring, ensuring their cloud infrastructure remains resilient against evolving threats.