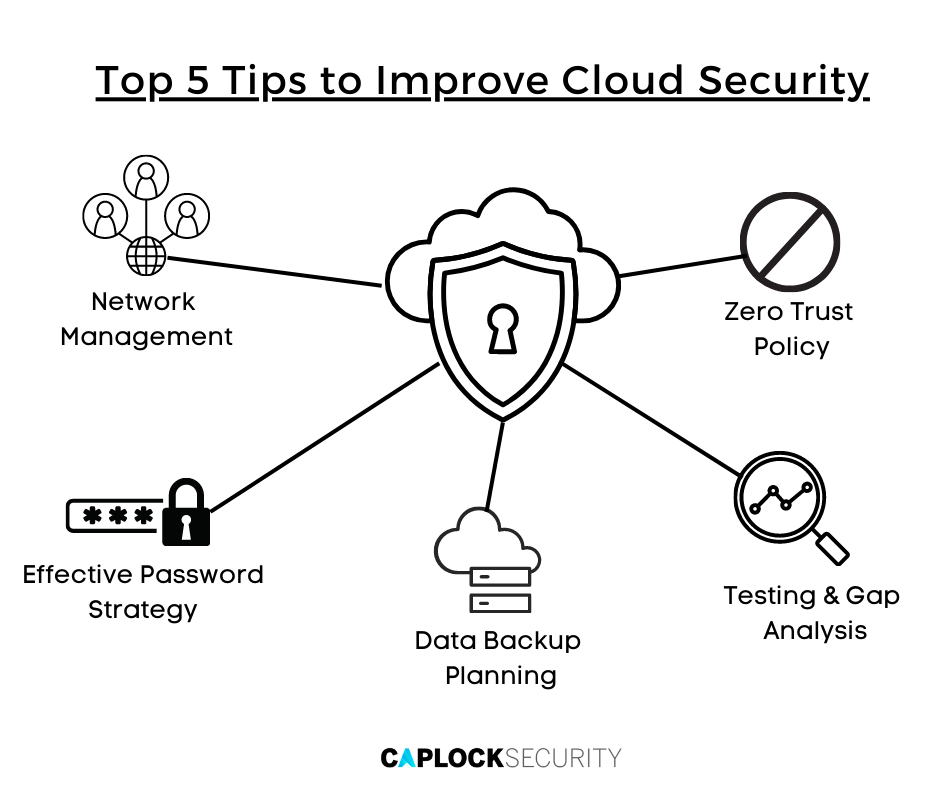
Top 5 Tips to Improve Cloud Security
There’s little doubt that the well-known public cloud service providers like Amazon, Google, and Microsoft provide a more secure environment than most organizations are capable of with their own in-house servers. Cloud providers are great at safeguarding information while it’s in their possession, but they can’t prevent the theft of credentials or the loss of data when it leaves the cloud and interacts with other third party systems.
The latter is something that occurs regularly in every business, as employees access, download, and transmit information from various devices, locations, and individuals. In most cases, it is human error that leads to a security breach, not a flaw in the cloud provider’s security protocols. Your cloud data is vulnerable due to stolen login passwords, dissatisfied workers, inadvertent deletions, unsecured wi-fi connections, and other staff errors.
What is Cloud Security?
Cloud security is a collection of rules, controls, procedures, and technology designed to safeguard your cloud-based applications, data, and systems. When the majority of workers operate remotely utilizing a mix of personal and professional equipment, a company’s “attack surface” expands, offering hackers additional opportunity.
CISA (Cybersecurity and Infrastructure Security Agency) disclosed in a recent alert that hackers have been using successful phishing attacks and brute force logins to compromise cloud security procedures.
In order to steal login credentials for cloud service accounts, attackers send emails containing malicious links. The emails and websites seem real, deceiving workers with these sophisticated phishing attempts. Unfortunately, any company’s lack of cyber hygiene practices often leaves the door open to hackers.
Many firms cannot distinguish between the obligations of their cloud service provider (CSP) and their own, exposing them to several dangers. The expansion of the cloud increases the potential attack surface of an organization. To further complicate matters, conventional security procedures sometimes fall short of cloud security requirements.
Five Tips to Improve Cloud Security in your Organization
The cloud enables enterprises to store and retrieve data in a flexible and scalable manner. Nevertheless, not all data is equivalent. Some purposes and forms of data are more sensitive than others and need unique cloud security considerations. Before settling on a cloud strategy, you should evaluate the sensitivity of your data.
The necessity for security increases in proportion to the sensitivity of the data. Organizations should also evaluate the evolution of their cloud strategy, since as data gets more sensitive, it is expected that the necessary security mechanisms should evolve.
Listed below are a few tips to protect your cloud procedures and workloads from cyberthreats.
1) Zero Trust Policy
The zero-trust security approach operates under the presumption that every effort by anything or anyone to join the network poses a risk. According to this theory of network security, neither users inside the network nor those outside it should be trusted unless their identification has been adequately verified. Zero-trust acknowledges that dangers, both inside and external to the network, are a constant. Network administrators’ thinking is influenced by these presumptions, which forces them to develop strict, reliable security mechanisms.
A zero-trust strategy requires rigorous identity verification before granting access to any person or device trying to connect to the network or application. This verification makes use of Multi-Factor Authentication (MFA), which requests multiple pieces of information from users before granting access. Network Access Control (NAC), which is used to prevent unwanted users and devices from connecting to a corporate or private network, is also a component of zero-trust. It guarantees that the network can be accessed by only authenticated users and approved, security-compliant devices.
2) Network Management
Network Security
Just like having more devices makes you more vulnerable, having additional unprotected wireless connections does the same. The data is more susceptible if your business provides free Wi-Fi for clients and a chat platform. Since organizations don’t have sensitive data on open networks, their security is frequently disregarded.
Automated Offboarding
The creation of automated processes for updating users and devices is an excellent concept. This makes sure that former personnel no longer have access and that new technology is protected.
- Consider it crucial to keep your system up-to-date with any potential software changes when it comes to your IT department.
- A system is more vulnerable to hacking if updates are not made in a timely manner.
- Software upgrades generally improve system performance and solve tricky-to-use features.
Encryption
Firms can take measures to further comply with compliance requirements, including data encryption. These relatively simple but essential procedures to help safeguard against a compromise include encrypting your health records, medical records, and other data, as well as making sure that devices are secure.
Since hackers won’t be able to decipher the code without a key, encryption automatically strengthens your cyber security perimeter. Every piece of financial and vital data is backed up and secured by an encryption code, keeping it safe in the event of a security breach. Access-level restrictions can be used to protect the data and regulate who might access it, preventing misuse.
3) Data Backup Planning
A plan for data backup is essential to any cloud security approach. A backup strategy can help guarantee that your data is retrieved and your activities can continue in the case of a data loss. Data loss may well be caused by a variety of factors, including hardware failures, software bugs, and human mistake.
Critical files can be manually copied onto backup media, but this can be time-consuming and error-prone. If at all possible, use an automated backup method. Some backup media, such as solid state drives and removable hard drives, are reusable. These media devices can deteriorate over time and after repeated backup cycles. As they age, it is especially important to test them for reliable restoration operations.
Companies should choose a backup solution that fulfills their requirements. Plans for data backup include of cloud-based backup, local backup, and offline backup.
- Internet-based data backup is a sort of cloud backup.
- Local backup is the process of backing up data to a local storage device, such as an external hard drive.
- Offline backup is a sort of data backup that is conducted in house.
4) Effective Password Strategy
The first line of protection against unwanted computer access is a password. Authentication should always need a password, regardless of device or operating system. Since the majority of cloud vulnerabilities are due to unauthorized access, one of the most critical things you can do to keep your data safe is to use strong passwords.
A strong password will not prevent an attacker from trying to obtain access, but it will slow them down and deter them. Because attackers may employ automated ways to guess a password, it is crucial to choose a password devoid of qualities that may make it susceptible.
Additionally, it is crucial to use unique passwords for each account. This prevents unauthorized access to your accounts if one of your passwords is ever compromised.
5) Testing and Gap Analysis
Organizations can conduct cloud security gap analysis, which is a comprehensive study that enables businesses to evaluate the gap between the actual situation of their information security and industry-specific needs. When you undertake a cloud security gap analysis, you get an understanding of your organization’s cybersecurity risks and vulnerabilities, allowing you to work on fix those security gaps.
Pen-testing, often known as penetrating testing, is a form of security test aimed to identify a system’s weaknesses. Both cloud-based and on-premises systems may be subjected to penetration testing to identify vulnerabilities.
Ethical Hacking may be used to obtain access to data or resources or to inflict system harm. Hackers often use automated techniques to identify and exploit vulnerabilities. They can help provide recommendations to increase the security of your system by discovering flaws that attackers might exploit.
These tests assist in enhancing system security and preventing data leaks within your cloud infrastructure. Organizations should regularly conduct penetration testing, gap analysis, and hacker simulations to identify security flaws.
Conclusion
Taking the necessary safeguards may make cloud computing a far more secure and cost-effective alternative. Following industry best practices for choosing, installing, deploying, and administering multi-cloud services will help you get the most out of cloud computing while protecting your sensitive data with a high degree of security.
Experienced security specialists may assist with the design and budgeting of an all-encompassing cloud computing strategy, as well as providing continuing monitoring to ensure security.
Outsourcing cybersecurity services and using sophisticated protection and monitoring technology can help ensure that your cloud security strategy is sound and that your customers’ data is safe, while allowing your own personnel to concentrate on other business matters.
Our team at Caplock Security is made up of devoted security professionals with years of experience in a variety of cybersecurity fields. Several of our clients have already used our assistance to improve their security standards, compliance requirements, and lower their risk. Our professionals can assist you in locating your security vulnerabilities and offer advice on how to fix them effectively.